Patch Management & Software Update Tools
These are the specialized categories within Patch Management & Software Update Tools. Looking for something broader? See all Cybersecurity, Privacy & Compliance Software categories.
How big is your team?
What's your budget situation?
What's your team's technical comfort level?
What's the ONE thing this tool must do well?

Avast Business Patch Management simplifies endpoint security for Windows environments by automating patch distribution through a master agent. Ideal for contractors, it supports numerous third-party apps to ensure software like Java and browsers remain secure, all within the centralized Avast Business Hub.
Best for Patch Management & Software Update Tools for Contractors
Expert Take
Avast Business Patch Management excels at taking the manual labor out of endpoint security for Windows-centric environments. Its ability to leverage a master agent for patch distribution minimizes network strain, while the comprehensive catalog of supported third-party applications ensures that notoriously vulnerable software like Java and browsers stay secure. The integration into the broader Avast Business Hub provides a unified, single-pane-of-glass experience for IT administrators.
Pros
- Automated 24/7 patch scanning
- Hundreds of third-party apps supported
- Master agent reduces network impact
- Centralized cloud Business Hub
Cons
- Windows OS strictly required
- History of corporate security breaches
- Lacks live installation progress prompts
Best for teams that are
- Small to medium businesses needing cost-effective patching.
- Organizations already using Avast Business security tools.
Skip if
- Organizations needing patch management for macOS devices.
- Large enterprises requiring advanced compliance workflows.
Best for teams that are
- Small to medium businesses needing cost-effective patching.
- Organizations already using Avast Business security tools.
Skip if
- Organizations needing patch management for macOS devices.
- Large enterprises requiring advanced compliance workflows.
Pros
- Automated 24/7 patch scanning
- Hundreds of third-party apps supported
- Master agent reduces network impact
- Centralized cloud Business Hub
Cons
- Windows OS strictly required
- History of corporate security breaches
- Lacks live installation progress prompts
Expert Take
Avast Business Patch Management excels at taking the manual labor out of endpoint security for Windows-centric environments. Its ability to leverage a master agent for patch distribution minimizes network strain, while the comprehensive catalog of supported third-party applications ensures that notoriously vulnerable software like Java and browsers stay secure. The integration into the broader Avast Business Hub provides a unified, single-pane-of-glass experience for IT administrators.
Absolute Resilience Security
Best for Patch Management & Software Update Tools for Private Equity Firms

Absolute Resilience for Security is an ideal solution for Private Equity firms that require robust patch management and software update tools. It proactively assesses patch health for known operating system and software vulnerabilities, ensuring the security and integrity of sensitive financial data.
Best for Patch Management & Software Update Tools for Private Equity Firms
Expert Take
Absolute Resilience Security is a specialized solution for Private Equity firms, offering robust patch management and proactive vulnerability assessments. It is recognized for its industry-specific capabilities and security focus, though pricing transparency is limited. The product's strong market credibility and usability make it a top choice in its category.
Pros
- Firmware-embedded persistence (undeletable agent)
- Self-healing of critical security apps
- Remote data wipe and device freeze
- FedRAMP Moderate Authorized
- Automated OS recovery (Rehydrate)
Cons
- Reporting delay for new devices
- Pricing not public on vendor site
- Occasional false positive device freezes
- Console can be laggy for some
Best for teams that are
- Organizations with highly mobile, remote, or distributed workforces
- Teams needing 'undeletable' firmware-embedded agents for strict compliance
- Enterprises requiring self-healing security controls and visibility
Skip if
- Companies with primarily fixed, on-premise server infrastructure
- Small businesses seeking a low-cost, basic patching utility
- Organizations that do not require device persistence or theft recovery
Best for teams that are
- Organizations with highly mobile, remote, or distributed workforces
- Teams needing 'undeletable' firmware-embedded agents for strict compliance
- Enterprises requiring self-healing security controls and visibility
Skip if
- Companies with primarily fixed, on-premise server infrastructure
- Small businesses seeking a low-cost, basic patching utility
- Organizations that do not require device persistence or theft recovery
Pros
- Firmware-embedded persistence (undeletable agent)
- Self-healing of critical security apps
- Remote data wipe and device freeze
- FedRAMP Moderate Authorized
- Automated OS recovery (Rehydrate)
Cons
- Reporting delay for new devices
- Pricing not public on vendor site
- Occasional false positive device freezes
- Console can be laggy for some
Expert Take
Absolute Resilience Security is a specialized solution for Private Equity firms, offering robust patch management and proactive vulnerability assessments. It is recognized for its industry-specific capabilities and security focus, though pricing transparency is limited. The product's strong market credibility and usability make it a top choice in its category.
Scalefusion Windows Patch Management
Best for Patch Management & Software Update Tools for Contractors

Scalefusion's Windows Patch Management software is a powerful tool for contractors, simplifying the process of managing, deploying, and securing software patches. Its efficiency, speed, and reliability are crucial in the fast-paced contracting industry where secure and smooth device performance is paramount.
Best for Patch Management & Software Update Tools for Contractors
Expert Take
Scalefusion Windows Patch Management excels in providing centralized and efficient patch management solutions tailored for contractors. Its strong market credibility, usability, and comprehensive reporting capabilities position it as a leading tool in its category.
Pros
- Automated third-party app patching
- Included in Enterprise plan ($4/mo)
- Support response under 4 minutes
- SOC 2 Type 2 & ISO 27001 certified
- Granular update scheduling control
Cons
- Initial setup can be complex
- Reporting analytics are somewhat basic
- Patching is paid add-on for Starter
- No built-in native VPN service
- Steep learning curve for beginners
Best for teams that are
- Organizations managing mixed OS mobile and desktop devices.
- Businesses needing unified MDM and kiosk lockdown features.
Skip if
- IT teams looking strictly for a standalone patch tool.
- Enterprises with complex, heavy server patching needs.
Best for teams that are
- Organizations managing mixed OS mobile and desktop devices.
- Businesses needing unified MDM and kiosk lockdown features.
Skip if
- IT teams looking strictly for a standalone patch tool.
- Enterprises with complex, heavy server patching needs.
Pros
- Automated third-party app patching
- Included in Enterprise plan ($4/mo)
- Support response under 4 minutes
- SOC 2 Type 2 & ISO 27001 certified
- Granular update scheduling control
Cons
- Initial setup can be complex
- Reporting analytics are somewhat basic
- Patching is paid add-on for Starter
- No built-in native VPN service
- Steep learning curve for beginners
Expert Take
Scalefusion Windows Patch Management excels in providing centralized and efficient patch management solutions tailored for contractors. Its strong market credibility, usability, and comprehensive reporting capabilities position it as a leading tool in its category.

Patch My PC addresses the critical needs of IT professionals in the SaaS industry by automating the packaging, testing, and deployment of thousands of third-party updates. This allows for efficient management of updates and patches, reducing the complexity and time consumption typically associated with these tasks.
Best for Patch Management & Software Update Tools for SaaS Companies
Expert Take
Patch My PC excels in automating patch management for SaaS companies, offering extensive application support and integration capabilities. Its market credibility is bolstered by third-party validation, and it provides a comprehensive user experience with detailed reporting. While it requires technical expertise, its value proposition remains strong for its target audience.
Pros
- Native Intune & ConfigMgr integration
- Massive catalog (3,000+ apps)
- Transparent public pricing
- ISO 27001 & SOC 2 certified
- Unlimited support included
Cons
- High minimum annual spend
- Requires Microsoft infrastructure
- Advanced reporting costs extra
- macOS update limitations
- No standalone patching agent
Best for teams that are
- Enterprises already using Microsoft Intune or SCCM for endpoint management.
- IT teams needing to automate third-party application updates seamlessly.
Skip if
- Organizations wanting a standalone patch tool without Microsoft infrastructure.
- IT environments that do not use Windows or Microsoft management tools.
Best for teams that are
- Enterprises already using Microsoft Intune or SCCM for endpoint management.
- IT teams needing to automate third-party application updates seamlessly.
Skip if
- Organizations wanting a standalone patch tool without Microsoft infrastructure.
- IT environments that do not use Windows or Microsoft management tools.
Pros
- Native Intune & ConfigMgr integration
- Massive catalog (3,000+ apps)
- Transparent public pricing
- ISO 27001 & SOC 2 certified
- Unlimited support included
Cons
- High minimum annual spend
- Requires Microsoft infrastructure
- Advanced reporting costs extra
- macOS update limitations
- No standalone patching agent
Expert Take
Patch My PC excels in automating patch management for SaaS companies, offering extensive application support and integration capabilities. Its market credibility is bolstered by third-party validation, and it provides a comprehensive user experience with detailed reporting. While it requires technical expertise, its value proposition remains strong for its target audience.
baramundi Patch Management
Best for Patch Management & Software Update Tools for Recruitment Agencies

baramundi Patch Management is a robust, automated solution designed to streamline the process of detecting, scheduling, deploying, and monitoring updates. This tool is ideal for recruitment agencies due to its ability to ensure the security and efficiency of their software systems, keeping sensitive data protected and operations running smoothly.
Best for Patch Management & Software Update Tools for Recruitment Agencies
Expert Take
baramundi Patch Management is a highly capable tool for recruitment agencies, offering strong automation and security features. While pricing transparency is limited, its robust capabilities in patch management and security make it a top choice in its category.
Pros
- Unified management of IT and OT/Industrial devices
- Pre-packaged, tested 3rd-party software updates
- Strong GDPR compliance and data privacy focus
- Modular pricing allows paying only for needed features
- Highly rated, responsive customer support
Cons
- Requires external SQL database license (hidden cost)
- Job-based workflow can be tedious for quick tasks
- Basic MDM features compared to market leaders
- On-premise infrastructure setup is heavier than SaaS
- Interface customization options are limited
Best for teams that are
- Medium to large orgs in IT, healthcare, or education needing broad endpoint management.
- IT teams needing to manage mixed OS environments (Windows, Mac, Linux).
- Organizations looking for flexible on-premises or virtual machine deployment options.
Skip if
- Small businesses with limited budgets due to external database and licensing costs.
- Teams with no programming experience, as complex script creation can be tricky.
- Users seeking a purely cloud-native solution without any server infrastructure.
Best for teams that are
- Medium to large orgs in IT, healthcare, or education needing broad endpoint management.
- IT teams needing to manage mixed OS environments (Windows, Mac, Linux).
- Organizations looking for flexible on-premises or virtual machine deployment options.
Skip if
- Small businesses with limited budgets due to external database and licensing costs.
- Teams with no programming experience, as complex script creation can be tricky.
- Users seeking a purely cloud-native solution without any server infrastructure.
Pros
- Unified management of IT and OT/Industrial devices
- Pre-packaged, tested 3rd-party software updates
- Strong GDPR compliance and data privacy focus
- Modular pricing allows paying only for needed features
- Highly rated, responsive customer support
Cons
- Requires external SQL database license (hidden cost)
- Job-based workflow can be tedious for quick tasks
- Basic MDM features compared to market leaders
- On-premise infrastructure setup is heavier than SaaS
- Interface customization options are limited
Expert Take
baramundi Patch Management is a highly capable tool for recruitment agencies, offering strong automation and security features. While pricing transparency is limited, its robust capabilities in patch management and security make it a top choice in its category.

Automox is a cloud-based, cross-platform automated solution designed to streamline patch management, configuration, and control across Windows, macOS, and Linux endpoints. It is specifically suited for SaaS companies, providing a single platform that integrates with existing IT infrastructure, reducing vulnerabilities and ensuring software is always up-to-date and compliant.
Best for Patch Management & Software Update Tools for SaaS Companies
Expert Take
Automox Endpoint Security excels in providing a comprehensive patch management solution tailored for SaaS companies. Its cross-platform capabilities and integration with existing IT infrastructure enhance its usability and effectiveness. While pricing transparency is limited, the product's robust security features and market credibility justify its premium positioning.
Pros
- Transparent pricing starting at $1/endpoint
- Cloud-native cross-platform patching (Win/Mac/Linux)
- SSO and MFA included in all plans
- Extensive library of pre-built automation Worklets
- CSA STAR and SOC 2 Type III certified
Cons
- No built-in automatic patch rollback
- Reporting lacks depth and customization
- Device grouping mechanism can be cumbersome
- Limited native integrations (e.g. Jira/Teams)
- Occasional agent stability issues reported
Best for teams that are
- Distributed organizations needing cloud-native, multi-OS patch management.
- IT teams wanting automated, policy-driven patching with custom scripts.
Skip if
- Highly secure, air-gapped networks without internet connectivity.
- Organizations requiring strict on-premises deployment and management.
Best for teams that are
- Distributed organizations needing cloud-native, multi-OS patch management.
- IT teams wanting automated, policy-driven patching with custom scripts.
Skip if
- Highly secure, air-gapped networks without internet connectivity.
- Organizations requiring strict on-premises deployment and management.
Pros
- Transparent pricing starting at $1/endpoint
- Cloud-native cross-platform patching (Win/Mac/Linux)
- SSO and MFA included in all plans
- Extensive library of pre-built automation Worklets
- CSA STAR and SOC 2 Type III certified
Cons
- No built-in automatic patch rollback
- Reporting lacks depth and customization
- Device grouping mechanism can be cumbersome
- Limited native integrations (e.g. Jira/Teams)
- Occasional agent stability issues reported
Expert Take
Automox Endpoint Security excels in providing a comprehensive patch management solution tailored for SaaS companies. Its cross-platform capabilities and integration with existing IT infrastructure enhance its usability and effectiveness. While pricing transparency is limited, the product's robust security features and market credibility justify its premium positioning.

Action1 is an all-in-one cloud-based patch management and vulnerability remediation tool specifically designed for SaaS companies. It offers an easy way to discover, prioritize, and fix vulnerabilities, which helps to prevent security breaches and ransomware attacks that can cripple SaaS operations.
Best for Patch Management & Software Update Tools for SaaS Companies
Expert Take
Action1 excels as a cloud-based patch management tool tailored for SaaS companies, offering comprehensive vulnerability assessment and automated patching. Its cloud-based architecture and continuous scanning capabilities make it a strong choice for distributed environments, despite limited customization options.
Pros
- First 100 endpoints free forever
- P2P distribution saves network bandwidth
- SOC 2 Type II & ISO 27001 certified
- Cloud-native setup in under 5 minutes
- Supports Windows, macOS, and Linux
Cons
- Reporting lacks executive summary visuals
- Limited remote control for macOS
- Potential conflicts with Intune update rings
- Paid tier starts at ~$4/endpoint/month
- No built-in ticketing system
Best for teams that are
- Small to mid-sized businesses benefiting from the free 200-endpoint tier.
- Distributed teams needing VPN-free, cloud-native patch management.
Skip if
- Buyers seeking transparent public pricing for deployments over 200 devices.
- Organizations needing on-premises, air-gapped network patching solutions.
Best for teams that are
- Small to mid-sized businesses benefiting from the free 200-endpoint tier.
- Distributed teams needing VPN-free, cloud-native patch management.
Skip if
- Buyers seeking transparent public pricing for deployments over 200 devices.
- Organizations needing on-premises, air-gapped network patching solutions.
Pros
- First 100 endpoints free forever
- P2P distribution saves network bandwidth
- SOC 2 Type II & ISO 27001 certified
- Cloud-native setup in under 5 minutes
- Supports Windows, macOS, and Linux
Cons
- Reporting lacks executive summary visuals
- Limited remote control for macOS
- Potential conflicts with Intune update rings
- Paid tier starts at ~$4/endpoint/month
- No built-in ticketing system
Expert Take
Action1 excels as a cloud-based patch management tool tailored for SaaS companies, offering comprehensive vulnerability assessment and automated patching. Its cloud-based architecture and continuous scanning capabilities make it a strong choice for distributed environments, despite limited customization options.
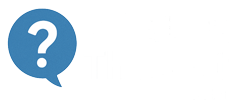
Qualys Patch Management is specifically designed for recruitment agencies that handle large volumes of sensitive data. The software provides timely vulnerability remediation and reduces risk by prioritizing and deploying patches across systems. The cloud-based solution allows remote patching, which is especially beneficial for agencies with distributed teams.
Best for Patch Management & Software Update Tools for Recruitment Agencies
Expert Take
Qualys Patch Management excels in providing a comprehensive patch management solution tailored for recruitment agencies. Its cloud-based architecture and ability to prioritize vulnerabilities make it particularly effective for distributed teams handling sensitive data. While it requires technical expertise, its robust capabilities and industry recognition justify its premium positioning.
Pros
- FedRAMP High Authorized security status
- Automated vulnerability-to-patch correlation
- Single agent for VMDR and patching
- Broad third-party application support
- Unified dashboard for all OSs
Cons
- No built-in driver update support
- Agent can cause high CPU usage
- Premium pricing with no transparency
- Reporting can be complex to configure
- Lacks rollback capabilities
Best for teams that are
- Large enterprises already utilizing the Qualys security suite and cloud agents.
- Security teams wanting to automate patching based on vulnerability asset tags.
- Organizations needing a single cloud-based platform for scanning and remediation.
Skip if
- Small businesses, as the pricing is considered high compared to alternatives.
- Environments where occasional false positive vulnerability flags cause disruptions.
- Massive environments where patch deployment speed is critical, as it can be slow.
Best for teams that are
- Large enterprises already utilizing the Qualys security suite and cloud agents.
- Security teams wanting to automate patching based on vulnerability asset tags.
- Organizations needing a single cloud-based platform for scanning and remediation.
Skip if
- Small businesses, as the pricing is considered high compared to alternatives.
- Environments where occasional false positive vulnerability flags cause disruptions.
- Massive environments where patch deployment speed is critical, as it can be slow.
Pros
- FedRAMP High Authorized security status
- Automated vulnerability-to-patch correlation
- Single agent for VMDR and patching
- Broad third-party application support
- Unified dashboard for all OSs
Cons
- No built-in driver update support
- Agent can cause high CPU usage
- Premium pricing with no transparency
- Reporting can be complex to configure
- Lacks rollback capabilities
Expert Take
Qualys Patch Management excels in providing a comprehensive patch management solution tailored for recruitment agencies. Its cloud-based architecture and ability to prioritize vulnerabilities make it particularly effective for distributed teams handling sensitive data. While it requires technical expertise, its robust capabilities and industry recognition justify its premium positioning.

Tenable Patch Management is a standout solution for staffing agencies, combining autonomous patching with leading vulnerability intelligence for a safer, more secure IT environment. It prioritizes patches based on their importance and urgency, thereby reducing the mean time to remediate (MTTR), a crucial feature for an industry that relies heavily on secure and efficient software solutions.
Best for Patch Management & Software Update Tools for Staffing Agencies
Expert Take
Tenable Patch Management excels in providing autonomous patching and leading vulnerability intelligence tailored for staffing agencies, ensuring efficient and secure IT environments. Its capability to prioritize patches based on urgency and importance is crucial for reducing MTTR, making it a top choice in its category.
Pros
- Automated correlation of VPR risk scores to patches
- Peer-to-peer distribution saves network bandwidth
- Unified view for Security and IT teams
- Supports Windows, Linux, and macOS patching
- Customizable rollback and pause controls
Cons
- Premium pricing model for full feature set
- Report customization can be complex
- Support response times vary by region
- Requires add-on to core vulnerability platform
- Steep learning curve for advanced features
Best for teams that are
- Existing Tenable Vulnerability Management customers
- Security teams bridging the scan-to-remediation gap
- Enterprises prioritizing risk-based patching
Skip if
- Small IT shops needing general endpoint management
- Teams not using Tenable for vulnerability scanning
- Organizations wanting a standalone IT management tool
Best for teams that are
- Existing Tenable Vulnerability Management customers
- Security teams bridging the scan-to-remediation gap
- Enterprises prioritizing risk-based patching
Skip if
- Small IT shops needing general endpoint management
- Teams not using Tenable for vulnerability scanning
- Organizations wanting a standalone IT management tool
Pros
- Automated correlation of VPR risk scores to patches
- Peer-to-peer distribution saves network bandwidth
- Unified view for Security and IT teams
- Supports Windows, Linux, and macOS patching
- Customizable rollback and pause controls
Cons
- Premium pricing model for full feature set
- Report customization can be complex
- Support response times vary by region
- Requires add-on to core vulnerability platform
- Steep learning curve for advanced features
Expert Take
Tenable Patch Management excels in providing autonomous patching and leading vulnerability intelligence tailored for staffing agencies, ensuring efficient and secure IT environments. Its capability to prioritize patches based on urgency and importance is crucial for reducing MTTR, making it a top choice in its category.
Heimdal Patch Management Tool
Best for Patch Management & Software Update Tools for Recruitment Agencies
Heimdal's Patch Management Software is an all-in-one solution for recruitment agencies. It automates patch management across multiple platforms including Microsoft, Apple, Linux, and third-party software, reducing downtime and improving system security. It's tailor-made to address the extensive IT needs of recruitment agencies, ensuring seamless workflow and data protection.
Best for Patch Management & Software Update Tools for Recruitment Agencies
Expert Take
Heimdal Patch Management Tool excels in providing a comprehensive solution tailored for recruitment agencies, offering robust cross-platform compatibility and automated patch deployment. It demonstrates strong market credibility through third-party recognition and offers significant value through its customizable settings and integration capabilities.
Pros
- Patches ready <4 hours from release
- P2P distribution saves bandwidth
- Sanitized updates remove adware
- SOC 2 Type II certified
- Integrates with Autotask/ConnectWise/HaloPSA
Cons
- Infinity Management excludes macOS
- Interface less intuitive than competitors
- Uninstall limited to MSI/QuietUninstallString
- New app support requires voting
- macOS updates cannot force restart
Best for teams that are
- Managed Service Providers (MSPs) and mid-sized companies seeking automated patching.
- IT teams needing to aggressively patch 3rd-party applications seamlessly.
- Organizations wanting a unified dashboard combining patching with EDR capabilities.
Skip if
- Large enterprises needing highly customized or complex patching workflows.
- Organizations that require extensive, highly detailed patch compliance reporting.
- Those needing to force specific updates manually, as it works best automatically.
Best for teams that are
- Managed Service Providers (MSPs) and mid-sized companies seeking automated patching.
- IT teams needing to aggressively patch 3rd-party applications seamlessly.
- Organizations wanting a unified dashboard combining patching with EDR capabilities.
Skip if
- Large enterprises needing highly customized or complex patching workflows.
- Organizations that require extensive, highly detailed patch compliance reporting.
- Those needing to force specific updates manually, as it works best automatically.
Pros
- Patches ready <4 hours from release
- P2P distribution saves bandwidth
- Sanitized updates remove adware
- SOC 2 Type II certified
- Integrates with Autotask/ConnectWise/HaloPSA
Cons
- Infinity Management excludes macOS
- Interface less intuitive than competitors
- Uninstall limited to MSI/QuietUninstallString
- New app support requires voting
- macOS updates cannot force restart
Expert Take
Heimdal Patch Management Tool excels in providing a comprehensive solution tailored for recruitment agencies, offering robust cross-platform compatibility and automated patch deployment. It demonstrates strong market credibility through third-party recognition and offers significant value through its customizable settings and integration capabilities.
Explore Categories
- Patch Management & Software Update Tools for Contractors
- Patch Management & Software Update Tools for Private Equity Firms
- Patch Management & Software Update Tools for Recruitment Agencies
- Patch Management & Software Update Tools for SaaS Companies
- Patch Management & Software Update Tools for Staffing Agencies
Loading comparison data…