
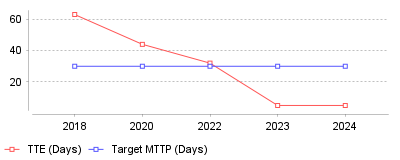
| Year | TTE (Days) | Target MTTP (Days) |
|---|---|---|
| 2018 | 63 | 30 |
| 2020 | 44 | 30 |
| 2022 | 32 | 30 |
| 2023 | 5 | 30 |
| 2024 | 5 | 30 |
This data demonstrates a drastic reduction in the Time-to-Exploit (TTE)—the average number of days it takes for a threat actor to weaponize a newly discovered vulnerability. In just a few years, this window has collapsed from over two months down to a mere five days, while the volume of published vulnerabilities has more than doubled [1].
At a macro level, this indicates that the traditional approach to patch management—such as relying on monthly scheduled patch cycles—is now fundamentally obsolete. With 80% of exploits being published before their corresponding CVEs are even officially released by the National Vulnerability Database (NVD), defenders are operating at a severe disadvantage [2]. Organizations can no longer wait for vendor patches or standard deployment windows without assuming extreme risk. At a micro level, this means IT and security teams are overwhelmed by an unprecedented volume of critical updates, forcing a pivot toward AI-driven automated patch deployment and virtual patching technologies [3].
This trend is vital because it redefines the baseline for corporate cybersecurity resilience and liability. The fact that the average Mean Time to Patch (MTTP) for critical vulnerabilities continues to hover around 15 to 30 days means that there is now a built-in exploitation window where businesses are entirely exposed to zero-day and rapid n-day attacks [4]. Failing to adapt to this compressed timeline frequently results in catastrophic ransomware infections, devastating data breaches, and subsequent regulatory penalties. Ultimately, closing this gap is the difference between business continuity and a major operational shutdown.
This acceleration is largely driven by the professionalization of cybercrime and the integration of artificial intelligence into the attacker's toolkit. Malicious actors are utilizing automated scanning, fuzzing, and AI-assisted vulnerability discovery to generate and distribute exploit scripts at machine speed [5]. Furthermore, the rise of specialized initial access brokers (IABs) and exploit marketplaces incentivizes hackers to monetize vulnerabilities immediately upon discovery. There is also a structural issue on the defensive side: complex enterprise IT/OT environments, legacy systems, and bottlenecks in change-management processes continually delay rapid patch deployment [6].
The era of leisurely software updates is officially over, replaced by a hyper-accelerated arms race between vulnerability disclosure and threat exploitation. To survive in this environment, organizations must transition from reactive, manual patching cadences to proactive, continuous threat exposure management. The most prominent takeaway is that leveraging automated patch management and compensating controls, such as network microsegmentation, is no longer a luxury—it is an absolute necessity to mitigate the inevitable delays in vendor patch cycles [7].
Global spending on information security will reach $212 billion in 2025. This represents a 15.1% increase from the previous year [1]. Within this allocation, the global patch management market will grow to $980 million in 2025, reaching $1.67 billion by 2029 [2]. Security leaders face immediate pressure to demonstrate returns on these investments. Forrester notes that almost 36% of a security leader's budget funds software purchases [3]. The North American region currently accounts for the largest revenue share in this sector, driven by national strategies and corporate infrastructure [4]. Analysts project sustained investment, with total market value expected to hit $377 billion by 2028 [1].
System updates represent defensive operations rather than administrative tasks. The U.S. Cybersecurity and Infrastructure Security Agency added 245 vulnerabilities to its Known Exploited Vulnerabilities catalog in 2025 [5]. This brought the threat list to 1,484 software defects [6]. Threat actors exploit these flaws faster than internal teams deploy fixes. Consequently, 60% of organizations experiencing a data breach trace the root cause back to an unpatched vulnerability [7]. Vulnerability research identifies a 30% increase in exploited catalog additions compared to the previous two-year average [8].
Defect volumes continue scaling beyond human capacity. Researchers cataloged over 21,500 Common Vulnerabilities and Exposures by mid-2025, representing an 18% increase from the prior year [9]. Analysts project the annual total could exceed 50,000 global disclosures [9]. Security teams must evaluate roughly 130 new defects every single day. Nearly 38% of these newly discovered flaws are classified as high severity [9]. Microsoft leads all vendors in catalog additions, contributing 39 exploited vulnerabilities in 2025 due to its market dominance [5].
Time remains the primary enemy of security operations. The median attacker dwell time fell to 10 days in 2024, down from 16 days two years prior [10]. Attackers need less time to locate external assets, breach the network, and encrypt files. In ransomware incidents, adversaries frequently deploy their payloads within 24 hours of initial access [11]. Operational standards dictate that security teams must detect and contain threats within 72 hours [10].
Defensive metrics show dangerous lag times across corporate environments. The average time required to detect and contain a breach sits at 241 days [12]. Mean time to remediate serves as the primary metric for measuring patch efficiency. IT administrators often delay patches to avoid network disruption. More than 80% of security professionals admit they postponed a patch to prevent downtime [7]. Another 80% of executives report discovering that patches they believed were deployed completely missed devices [7].
Delaying updates creates fatal exposure windows. Security vendors tracked 161 vulnerabilities actively exploited in the wild during the first half of 2025 [9]. The mean time for attackers to weaponize a new flaw dropped to just five days [7]. Administrators face a one-in-four chance that a vulnerability will suffer active exploitation before they complete their testing protocols [7]. Organizations evaluating software update infrastructure must prioritize automated capabilities to close this structural gap.
Legacy code compounds the remediation urgency. Federal regulators do not just track new exploits. In 2025, the government added 94 older vulnerabilities to its tracking catalog, representing a 34% increase in the resurrection of past threats [5]. The oldest vulnerability listed involves a Microsoft privilege escalation flaw from 2002 that operators still actively abuse [5].

Regulators drastically altered reporting requirements regarding software flaws. The Securities and Exchange Commission mandates that public companies disclose cybersecurity incidents via Form 8-K within four business days [13]. Corporations must also detail their risk strategies and oversight roles in annual 10-K filings [14]. The rules apply equally to newly discovered zero-day attacks and breaches stemming from known software.
Transitioning to public disclosure proved chaotic for security teams. Initial filings showed widespread confusion regarding materiality thresholds. During 2024, many companies submitted reports for non-material events to avoid penalties, prompting the SEC to issue guidance [15]. Furthermore, an independent review of 10-K filings revealed that only 24 documents explicitly outlined assessment methods [16]. Most companies relied on generic language rather than explicitly describing their patching procedures.
Federal authorities demonstrated their willingness to litigate disclosure failures. The SEC charged four technology firms in October 2024 for publishing misleading statements regarding the SolarWinds intrusion [14]. The agency also pursued a lawsuit against SolarWinds and its Chief Information Security Officer. The original complaint accused the executives of overstating their security practices while minimizing network risks [17].
Although officials eventually agreed to dismiss the remaining claims against SolarWinds in late 2025, the legal action forced a permanent change in corporate governance [17]. The dismissal does not grant immunity from future enforcement. The commission explicitly stated the decision was an exercise of discretion and did not reflect its broader stance on executive accountability [18]. Corporate boards must ensure their patching records match the claims made to investors.
Data breaches exact financial penalties upon organizations. The global average cost of a network intrusion reached $4.44 million in 2025 [19]. In the United States, that figure surged to a record $10.22 million per incident [20]. Incident response, forensic investigations, system restoration, and regulatory fines drive these corporate expenditures [21].
UnitedHealth Group's breach perfectly illustrates the cost of unpatched infrastructure. Attackers compromised a legacy server belonging to the company's Change Healthcare subsidiary in early 2024 [21]. The intrusion disrupted medical billing nationwide and exposed personal records belonging to 192.7 million individuals [22]. The perpetrators exploited an external server that lacked multifactor authentication and security updates [21].
Financial devastation escalated rapidly for the company. UnitedHealth initially estimated the cyberattack would cost $1.6 billion [23]. By the end of 2024, response costs and disruption losses totaled $2.87 billion [24]. The final accounting at the close of the fiscal year pushed the annual loss to $3.09 billion [25]. The company disbursed over $9 billion in emergency loans to medical providers affected by the network outage [23].
Supply chain vulnerabilities amplify these financial impacts exponentially. Progress Software discovered a zero-day flaw in its MOVEit file transfer application in May 2023 [26]. The Cl0p extortion group exploited this injection vulnerability to compromise 2,773 organizations and steal data from 95.7 million people [27]. Impacted entities included Maximus, Delta Dental, and the Louisiana Office of Motor Vehicles [27].
Legal liabilities compound the technical costs associated with software vulnerabilities. Following the MOVEit exposure, Progress Software faced at least 144 lawsuits and multiple federal investigations [28]. IBM data indicates that third-party compromises increase the total cost of a security breach by nearly $240,000 [26]. Such financial exposure forces investment firms to scrutinize the technical debt of their portfolio assets. Consequently, updating network systems at investment firms requires centralized visibility to prevent portfolio contagion.
Different industries face distinct operational hurdles when deploying updates. Healthcare organizations suffer the highest breach costs, averaging $7.42 million per incident [12]. Hospitals operate medical devices that cannot undergo reboots without endangering patient safety. Consequently, healthcare IT teams average 93 days just to detect an intrusion [29]. Criminals monetize this delay by selling patient records on illegal markets for $280 per file [29].
Software providers grapple with entirely different structural weaknesses. Cloud misconfigurations and unpatched programming interfaces allow attackers to bypass perimeter defenses. The average cost of a cloud breach sits at $4.18 million [30]. Technology vendors must secure their staging environments while pushing updates to clients. Proper vulnerability management at tech platforms demands automated pipelines that integrate directly with integration workflows.
Decentralized workforces introduce severe endpoint vulnerabilities. Remote employees frequently connect to corporate networks using unpatched personal devices. Threat actors exploit these distributed endpoints to access central databases. Identity-based attacks exploiting weak credentials accounted for a significant portion of network intrusions in 2025 [31]. Administrators managing contingent workers need agent software to force updates over residential connections. Evaluating remote update deployment tools for distributed teams is a priority for organizations relying on remote labor.
Recruitment firms manage exceptional volumes of personal information. Resumes contain employment histories, contact details, and financial expectations. A database breach exposes thousands of individuals to severe identity theft risks. Hiring businesses must ensure their database software receives immediate security revisions. Implementing system maintenance for agency networks protects this targeted data from extraction.
Machine learning systems actively accelerate both threat deployment and remediation. Attackers use generative algorithms to write malicious code and automate phishing campaigns. Approximately 16% of network breaches in 2025 involved adversaries using artificial intelligence [30]. Generative software reduces the time required to craft a phishing email from 16 hours to five minutes [30]. These automated tools allow amateur hackers to rapidly discover and exploit legacy servers.
Unsanctioned software further complicates network defense. Employees routinely adopt unauthorized generative applications without IT approval. These isolated deployments create dangerous blind spots. Breaches involving unsanctioned artificial intelligence cost organizations $4.63 million on average, exceeding standard incident costs by $670,000 [30]. Furthermore, 97% of incidents related to machine learning occurred at organizations lacking basic access controls for these specific tools [20]. IT departments cannot patch software they do not know exists.
Defensive automation provides significant financial protection. Organizations relying heavily on security automation reduced their incident lifecycle by 80 days [20]. These companies also saved an average of $1.9 million per breach compared to peers lacking automated controls [20].
Security vendors recognize this shifting requirement. Software manufacturers abandoned basic severity scores in favor of risk analysis. Rapid7 introduced an automated scoring feature to its Exposure Command product in 2024 to supplement missing government data [32]. These predictive models analyze external threat intelligence to push emergency patches ahead of scheduled maintenance windows.
Platform integration helps solve the visibility problem. Vulnerability scanners now feed directly into deployment engines. If a scanning tool identifies a vulnerability like the Citrix Netscaler flaw, the platform automatically prioritizes the remediation patch [33]. Connecting detection capabilities with remediation engines is critical for minimizing the attacker dwell time.
Standalone update servers no longer satisfy security requirements. Organizations increasingly demand endpoint platforms that combine vulnerability scanning, patch deployment, and post-attack recovery. Modern security teams want broad visibility rather than isolated metric dashboards. Endpoint security solutions evolved from single-function products into unified response systems [34].
Major technology firms dominate the known vulnerability metrics. Microsoft accounted for 39 of the vulnerabilities added to the federal catalog in 2025 [5]. Independent research from VulnCheck tracked 717 exploited flaws across 410 unique vendors during a similar timeframe [35]. The most frequently targeted products included Microsoft Windows, Google Chrome, and Apple IOS [35]. This diversity of vulnerable software dictates that administrative tools must support extensive application catalogs, not just primary operating systems.
Ransomware specifically targets perimeter security infrastructure. In 2025, federal authorities linked 304 exploited vulnerabilities directly to extortion groups [8]. Cybercriminals frequently target edge devices like virtual private network servers and firewalls manufactured by Cisco, Ivanti, and Fortinet [35]. Attackers know that patching a firewall often requires scheduling network downtime, giving them ample time to deploy their exploits.
Network complexity guarantees that patching remains difficult. Organizations operate hybrid architectures spanning local servers, remote laptops, and cloud containers. Software must verify endpoint health before granting access to central data. Compliance and security software applications now actively block devices that lack the latest security updates. Administrators must balance strict access controls against the operational reality that testing software patches takes time.
Automation will define the next operational era. Regulatory scrutiny will continue to punish organizations that ignore software maintenance. The sheer volume of new vulnerabilities makes manual deployment impossible. Managing 50,000 potential software defects annually requires machine-driven prioritization [9].
Corporate boards must fund intelligent deployment systems. Relying on scheduled maintenance windows guarantees network exposure. Attackers automate their exploits; defenders must automate their patches. The financial penalties of failure—demonstrated by massive losses at major corporations—leave security leaders with no other viable strategy.