
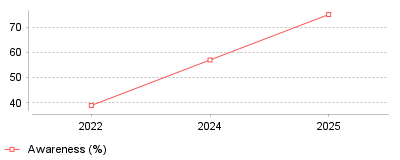
| Year | Awareness (%) |
|---|---|
| 2022 | 39 |
| 2024 | 57 |
| 2025 | 75 |
This trend data illustrates a dramatic surge in both consumer awareness and enterprise deployment of passkeys as a primary authentication method. Between 2022 and 2025, global consumer awareness of passkeys skyrocketed from 39% to 75% [1]. Concurrently, the number of the world's top 100 websites supporting passkey logins more than doubled, jumping from 20% in 2024 to 48% by mid-2025 [2].
At a micro level, this means individual users are experiencing far less friction during sign-in, with login times reportedly dropping by 73% when using passkeys compared to traditional multi-factor authentication [3]. Users are no longer burdened by remembering complex passwords, which directly reduces cart abandonment rates and login fatigue. On a macro industry scale, Identity and Access Management (IAM) vendors are rapidly pivoting their roadmaps to prioritize FIDO2 and WebAuthn standards. Organizations are systematically deprecating shared-secret authentication to protect their bottom lines, fundamentally altering the baseline security expectations for consumer-facing and enterprise applications.
The transition to passkeys is critical because compromised credentials remain the primary vector for data breaches worldwide, involved in an overwhelming majority of web application attacks [4]. Passkeys offer a phishing-resistant alternative that binds the credential to the user's specific device, neutralizing man-in-the-middle and traditional phishing attacks. Eliminating passwords also yields massive operational cost savings for IT departments by drastically cutting down on password-reset helpdesk tickets, which historically account for a massive chunk of IT support requests [5].
The acceleration of this trend was largely catalyzed by coordinated efforts from tech giants like Apple, , and Microsoft to integrate native passkey support directly into their operating systems and browsers [6]. This ecosystem-wide alignment removed the technical friction that previously hindered passwordless adoption. Furthermore, the relentless surge in sophisticated, AI-driven phishing and credential-stuffing attacks has forced both consumers and enterprises to seek more resilient security measures. Regulatory pressures and high-profile security incidents have likely also pushed executive boards to mandate stronger, phishing-resistant authentication frameworks to protect user data and corporate assets.
The data unequivocally confirms that the passwordless future is no longer just a theoretical concept, but an active, widespread reality reshaping the IAM landscape. As major platforms make passkeys the default authentication method, companies that delay adoption risk higher security vulnerabilities and worsening user experiences. The prominent takeaway is that organizations must immediately integrate passkey infrastructure, or they will face competitive disadvantages in both customer retention and overall cybersecurity posture.
IBM reported the global average cost of a data breach reached $4.88 million in 2024. [1] This figure represents a 10% increase from 2023, marking the largest annual jump since the pandemic. [2] Post-breach recovery activities and severe business disruption drove this financial penalty higher. [3] Breached organizations face operational downtime, accelerated customer churn, and massive regulatory fines. [4] The United States maintained the highest geographic breach cost at $9.36 million per incident. [5]
Corporate security budgets expand rapidly to address these systemic vulnerabilities. The global market for identity and access management software reached $18.3 billion in 2024. [6] Stratview Research projects this sector will climb to $70.5 billion by 2034. [6] North America currently holds the largest regional share of this spending. [7]
Security teams struggle specifically with stolen credentials. These compromised logins acted as the initial attack vector in 16% of all recorded breaches during 2024. [5] Incidents involving stolen credentials required an average of 292 days to identify and contain. [8] This delayed detection makes credential-based attacks the longest-lasting breach category monitored by IBM. [8]
Financial damages escalate further when sensitive data resides across multiple cloud environments. Forty percent of breaches involved distributed data sources. [4] These persistent visibility gaps contributed directly to a 27% rise in intellectual property theft over a single year. [9] The explicit cost of stolen intellectual property records jumped to $173 per record. [2] Organizations also experienced a 22.7% increase in regulatory fines exceeding $50,000. [4]
Involving law enforcement lowered breach costs by 20%. [4] Most ransomware victims who contacted authorities avoided paying ransoms entirely. [9]
Malware no longer serves as the primary threat to enterprise networks. Threat actors simply log in using stolen usernames and passwords. CrowdStrike found that 75% of attacks used to gain initial network access in 2023 were entirely malware-free. [10] Interactive intrusions featuring hands-on keyboard activity increased 60% year over year. [11]
The Identity Defined Security Alliance reported that 90% of organizations experienced an identity-related incident during the past year. [12] Eighty-four percent of these affected companies suffered direct business impacts, up from 68% the previous year. [12] Phishing remained the most common identity incident, affecting 69% of surveyed organizations. [13] The Anti-Phishing Working Group tracked nearly five million phishing attacks in late 2023. [12]
Attackers increasingly target cloud infrastructure rather than on-premises servers. CrowdStrike observed a 75% increase in cloud intrusions overall. [11] Threat actors exploit valid credentials to navigate through cloud directories undetected. [11] This tactical shift forces companies to rethink their broad cybersecurity, privacy and compliance software investments. Perimeter firewalls offer zero protection when an attacker authenticates with a legitimate administrative password.
Access broker advertisements selling valid credentials jumped 20% on illicit forums in 2023. [10] Cybercrime groups purchase these logins to bypass initial network defenses. Once authenticated, attackers establish persistence and escalate privileges using native administrative tools. [10] Over 50% of observed attack techniques in the MITRE ATT&CK framework directly target user identities. [14]
Compromised privileged identities accounted for 33% of security incidents in the 2024 Identity Defined Security Alliance report. [12] Breaching a network via a privileged account gives an attacker fast-tracked access to sensitive databases.

Microsoft faced a critical vulnerability in July 2025 involving its Entra ID platform. [15] Security researcher Dirk-jan Mollema discovered an authentication failure in the legacy Azure AD Graph API. [16] This flaw allowed attackers to exploit internal service tickets. [17] Microsoft refers to these tickets internally as "Actor tokens." [15]
The vulnerability received a maximum CVSS score of 10.0. [18] The legacy API failed to validate the originating tenant of the token. [15] An attacker could generate a valid token in their own test environment and use it to impersonate a Global Administrator in any other organization. [17] This exploit completely bypassed multi-factor authentication. [19] It circumvented Conditional Access policies and generated no audit logs in the victim tenant. [17] Microsoft deployed a global hotfix three days after the initial disclosure. [20]
Semperis researchers discovered another vulnerability known as nOAuth in Microsoft Entra ID. [21] This flaw exploited application configurations that permitted unverified email claims as user identifiers. [21] Attackers needed only an Entra tenant and a target email address to assume control of SaaS accounts. [21]
Okta experienced multiple severe operational incidents during recent months. Hackers breached Okta's customer support system in October 2023. [22] The attackers compromised an employee's personal Google account to install malware on a corporate laptop. [23] They then extracted HTTP Archive files submitted by Okta customers. [23] These troubleshooting files contained active session cookies. [23]
One hundred thirty-four customers suffered exposure during this support system hack. [23] Targeted organizations included BeyondTrust, Cloudflare, and 1Password. [23] BeyondTrust detected an attacker attempting to breach their Okta environment using a valid session cookie just 30 minutes after uploading the support file. [23] Okta agreed to a $60 million shareholder settlement in July 2024 regarding this incident. [24]
Threat actors launched massive credential stuffing attacks against Okta's cross-origin authentication feature in April 2024. [22] Attackers routed millions of automated login requests through residential proxy networks and the Tor anonymity network. [25] This infrastructure allowed attackers to mask their origin while testing previously stolen passwords against Okta customer tenants. [25]
Machine identities currently outnumber human identities by 20 to 1 in typical enterprise environments. [26] This ratio climbs to 500 to 1 in cloud-native infrastructures. [26] Non-human identities include application programming interfaces, virtual machines, automated scripts, and connected hardware sensors. [7]
The global machine identity management sector generated $3.6 billion in 2024. [7] DataIntelo projects this market will reach $21.9 billion by 2033. [7] Cloud computing adoption accelerates this growth. [27] Software applications continuously request access to databases and storage buckets without human intervention. [7]
Security coverage for these automated connections remains dangerously low. Gartner analysts surveyed 335 identity leaders in late 2024. [28] These leaders reported their teams manage only 44% of their organization's machine identities. [28] Developers often create service accounts with excessive permissions and fail to rotate the cryptographic keys. [26]
Managing automated system credentials proves especially difficult when configuring access control systems for financial auditing teams. Auditing scripts frequently pull ledger data across multiple databases. If an attacker compromises an unmonitored script, they gain immediate read access to sensitive financial records.
North America captured 34.1% of the machine identity market share in 2023. [29] Companies in this region invest heavily to secure connected devices and maintain regulatory compliance. [29] Next-generation machine security platforms must automate credential rotation and enforce strict access controls based on continuous behavioral monitoring. [26]
Gartner predicts 60% of enterprises will phase out remote access virtual private networks in favor of zero-trust network access. [30] This transition requires precise identity validation for every machine request.
The United States Securities and Exchange Commission adopted strict cybersecurity disclosure rules in July 2023. [31] These regulations completely altered how public companies handle data breach reporting. Registrants must now disclose material cybersecurity incidents on Item 1.05 of Form 8-K. [31]
Companies have exactly four business days to file this public disclosure. [31] The compliance clock starts when the company determines the breach is material, not when the breach initially occurred. [32] Organizations can only delay this filing if the United States Attorney General determines immediate disclosure poses a substantial risk to national security. [31] Foreign private issuers face similar requirements on Form 6-K. [31]
These compressed reporting timelines change how businesses configure their authentication platforms. Organizations require precise forensic data to determine materiality within hours. This urgency affects all sectors, dictating how specialized login security tools used by building firms must retain access logs for rapid review.
The SEC also requires annual disclosures regarding cyber risk management on Regulation S-K Item 106. [31] Companies must describe their specific processes for assessing and managing material risks from cybersecurity threats. [33] They must detail the board of directors' oversight role and management's expertise in assessing cyber threats. [33]
HealthEquity filed a Form 8-K in July 2024 following a partner account compromise. [34] The breach exposed protected health information for millions of customers. [34] Prior to the SEC mandate, companies often waited months to formally announce similar incidents.
The European Union implemented the NIS2 Directive, mandating a strict three-phase reporting structure. [35] Organizations must issue an early warning notification within 24 hours of detecting a significant incident. [35] They must follow this with a detailed notification within 72 hours. [35]
Healthcare organizations spent $9.77 million per data breach in 2024. [8] This sector maintained the highest average breach cost for the fourteenth consecutive year. [8] Medical records command premium prices on illicit markets. The life-safety implications of hospital ransomware attacks also force administrators into expensive recovery operations.
Financial services companies faced average breach costs of $6.08 million. [36] Malicious actors target banks to initiate fraudulent wire transfers. Customer trust vanishes rapidly if financial institutions fail to secure client data. Deploying proper authentication platforms for property brokers remains a critical mandate to protect wire instructions during real estate closings.
Finance firms mitigate these costs through dedicated security investments. IBM found that financial companies with dedicated incident response teams saved $248,000 annually. [36] Firms deploying advanced identity solutions saved an additional $223,000 per year. [36] However, mega-breaches involving more than 50 million records pushed average recovery costs to $375 million. [36]
The cybersecurity skills gap worsens this financial impact. Over half of breached organizations reported severe staffing shortages. [8] These shortages corresponded to an average increase of $1.76 million in breach costs. [8]
Speed determines the final financial damage of an intrusion. CrowdStrike calculated the average eCrime breakout time at 62 minutes in 2023. [10] Breakout time measures how quickly an attacker moves laterally after gaining initial host access. [37] The fastest recorded breakout occurred in just 2 minutes and 7 seconds. [37]
Attackers move quickly because they use legitimate credentials. Security analysts cannot easily distinguish between a malicious actor and a genuine employee. Implementing access platforms built for digital advertising teams requires careful balancing. Marketing agencies need remote access to client social media accounts, but strict geographic conditional access policies must block suspicious offshore logins.
Gartner expects 30% of enterprises will reject isolated biometric authentication by 2026. [38] Artificial intelligence allows attackers to generate synthetic facial images and convincing voice clones. Presentation attacks and injection attacks can easily bypass basic facial recognition software. [38] Gartner reported injection attacks increased 200% in 2023. [38]
Security leaders must integrate device identification and behavioral analytics into their access workflows. [38] Organizations cannot rely on a single verification method. Passwordless authentication continues to gain corporate support as a phishing-resistant alternative. [39] An Identity Defined Security Alliance survey showed 81% of identity professionals view passwordless technology as a viable solution. [39]
Regulatory changes in Europe push this transition forward. The eIDAS 2.0 regulation drives the adoption of digital identity wallets and biometric document verification. [40] Major technology companies, including Microsoft, announced plans to expand passkey support to eliminate passwords entirely. [40]
Organizations currently use an average of 45 different cybersecurity tools. [28] Managing this tool sprawl creates operational friction. Security architects must consolidate core controls to improve data portability. [28]
Automation directly reduces the financial damage of cyber attacks. IBM found organizations using artificial intelligence for security prevention lowered their average breach costs by $2.22 million compared to companies relying on manual processes. [3] Organizations deploying artificial intelligence extensively averaged breach costs of $3.84 million. [3] Companies without automation faced costs of $5.72 million. [3]
The future of access management relies on continuous risk assessment. Static passwords and one-time multi-factor codes fail to stop sophisticated adversaries. Systems must evaluate user behavior, location, and device posture throughout the entire active session to detect anomalous activity. [30]