CNAPP market will surge from $8.28 billion to $71 billion by 2035
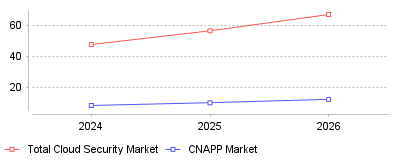
Global Market Size Trajectory (USD Billions)
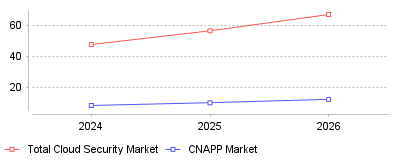
| Year | Total Cloud Security Market | CNAPP Market |
|---|
| 2024 | 47.8 | 8.28 |
| 2025 | 56.69 | 10.07 |
| 2026 | 67.24 | 12.25 |
The Consolidation Imperative: The Rise of CNAPP and DSPM
What is this showing
This trend demonstrates a massive architectural pivot in the cybersecurity landscape, where enterprises are aggressively abandoning siloed, single-purpose security tools in favor of unified Cloud-Native Application Protection Platforms (CNAPP) and Data Security Posture Management (DSPM) systems [1]. Survey data indicates that modern organizations are currently juggling an average of 17 discrete cloud defenses, leading to severe "tool sprawl" and fragmented data visibility [1]. As a direct response to this operational chaos, approximately 70% of Chief Information Security Officers (CISOs) are actively consolidating their software solutions into integrated platforms to regain control over their rapidly expanding multi-cloud environments [2].
What this means
On a micro level, this consolidation fundamentally transforms the day-to-day operations of security teams. By integrating code scanning, cloud security posture management (CSPM), and runtime protection into a single workflow, analysts experience significantly less context switching and can resolve incidents exponentially faster [3], [1]. Organizations utilizing integrated CNAPP solutions have reported reducing their security-related operational overhead by nearly 30% compared to those reliant on disparate, overlapping tools [3]. On a macro industry scale, this demand for end-to-end visibility is triggering a massive wave of market consolidation, mergers, and acquisitions. Large hyperscalers and dominant security vendors are acquiring smaller, specialized startups—such as 's $32 billion pursuit of Wiz and Rubrik's acquisition of Laminar—to build comprehensive platform ecosystems [4]. Consequently, the global CNAPP market, valued at roughly $8.28 billion in 2024, is projected to surge past $71 billion by 2035, fundamentally narrowing the competitive landscape for standalone security vendors [5], [4].
Why is this important
This transition is critical because the attack surface of modern enterprises has expanded beyond human capacity to monitor manually, largely due to the proliferation of multi-cloud architectures and generative AI [6]. With 88% of organizations now operating across hybrid or multi-cloud setups, consistent policy enforcement has become nearly impossible using legacy perimeter-based defenses [7], [6]. Furthermore, industry experts predict that through 2025, 99% of cloud security failures will be the direct result of customer-driven misconfigurations, highlighting the urgent need for automated, intelligent guardrails that only unified platforms can provide [8]. Without consolidated visibility, security teams face critical blind spots, allowing threats like AI-driven autonomous agents and credential theft to persist undetected in fragmented cloud environments [9], [10].
What might have caused this
The root cause of this trend likely traces back to the rapid, often chaotic digital transformations organizations undertook during the pandemic, immediately followed by the explosion of enterprise AI adoption [11]. In the rush to migrate workloads to the cloud, development teams rapidly deployed diverse infrastructure components, prompting security teams to quickly buy niche, point-solution tools to patch immediate vulnerabilities [1]. Over time, this reactionary procurement strategy created a tangled web of overlapping tools that generated thousands of daily alerts—many of them false positives—resulting in severe "alert fatigue" and burnout among cybersecurity professionals [8], [3]. Additionally, the increasing stringency of global data privacy regulations has forced organizations to seek holistic platforms that can simultaneously guarantee compliance, maintain data residency, and enforce threat detection across complex architectures [12]. Ultimately, the financial pressure of maintaining dozens of disparate software licenses combined with the operational friction of siloed workflows created an unsustainable breaking point for enterprise security budgets.
Conclusion
The era of "grafting" isolated security tools onto diverse cloud infrastructure is decisively ending, replaced by a mandate for unified, predictive resilience. As threat actors increasingly leverage autonomous AI to exploit minor misconfigurations across sprawling multi-cloud environments, organizations must adopt consolidated platforms like CNAPP and DSPM to survive and effectively scale [13]. The most prominent takeaway is that platform consolidation is no longer merely a cost-saving procurement strategy; it is a foundational necessity for achieving the real-time visibility, automated remediation, and operational efficiency required to secure the future of digital business.
The Valuation Premium of Cloud Defenses
Alphabet offered $23 billion to acquire security startup Wiz in July 2024
[1]. Chief Executive Officer Assaf Rappaport rejected the proposal shortly after. The startup instead announced intentions to pursue an initial public offering upon reaching $1 billion in annual recurring revenue. Wiz crossed $500 million in recurring revenue that same month, representing a 103% year-over-year growth rate
[2].
The rejected offer would have marked the largest acquisition in Google's corporate history. It eclipsed the $12.5 billion the search giant paid for Motorola Mobility in 2012
[3]. Tech industry analysts observed this premium valuation reflects an urgent corporate mandate to secure distributed computing networks. Market capitalizations across the sector reflect this urgency. Threat detection vendor CrowdStrike traded at an $85 billion valuation in late 2024, while incumbent Palo Alto Networks reached a $127 billion market capitalization
[4].
Corporate spending on defensive software continues to outpace broader technology investments. Gartner predicts cloud security budgets will grow from $9.0 billion in 2024 to $22.6 billion by 2028
[5]. This represents a 25.9% compound annual growth rate, making it the fastest-growing segment within the information technology security sector. Global end-user spending on information security will total $212 billion in 2025 and reach $240 billion by 2026
[6].
Chief information security officers face mounting pressure to protect hybrid networks against automated attacks. Network infrastructure protection spending will jump from $31.3 billion in 2024 to $51.2 billion in 2028
[5]. Organizations cannot afford to leave artificial intelligence workloads exposed. Network hardware purchases will increase concurrently, rising from $21.7 billion in 2024 to $32.8 billion over the same four-year period.
Breach Economics and the Cost of Exposure
Data compromises exact heavier financial tolls than ever before. IBM reported the global average cost of a data breach reached $4.88 million in 2024
[7]. This figure represents a 10% increase from 2023. Post-breach customer support, lost business opportunities, and regulatory fines primarily drove this spike.
Geography and industry vertical heavily influence the final cost. United States companies suffered the highest average breach cost at $9.36 million per incident
[8]. Healthcare organizations led all sectors, paying $9.8 million per incident. Financial services firms ranked second, facing average remediation bills of $6.08 million
[9].
Scale amplifies these financial damages exponentially. Mega breaches involving 50 million records or more resulted in average costs of $375 million
[9]. Security teams needed an average of 292 days to identify and contain incidents where data was scattered across public servers, private servers, and on-premises hardware
[10].
Specific attack vectors determine the timeline and expense of recovery. Compromised credentials initiated 16% of all tracked breaches, taking nearly 10 months to resolve
[7]. Phishing attacks caused 15% of breaches and cost organizations $4.76 million on average
[10]. Malicious insider actions represented only 7% of events but proved to be the most expensive vector at $4.99 million per incident
[8].
Retail operations present lucrative targets for these credential-based attacks. Payment processing systems contain highly liquid data assets. This risk profile explains why
cloud security platforms for ecommerce businesses emphasize identity access management and strict transaction logging. Online merchants lose direct sales revenue for every minute their portals remain offline during an incident response protocol.
Shadow data complicates these recovery efforts. Unmanaged data sources contributed to 35% of all breaches in 2024
[10]. Incidents involving these invisible data assets cost 16% more to remediate than standard breaches. IT departments cannot protect server instances they do not know exist, allowing attackers to establish persistent footholds in forgotten testing environments.
Regulatory Friction and the 96-Hour Window
The United States Securities and Exchange Commission fundamentally altered corporate incident response protocols in late 2023. The agency enacted new rules requiring public companies to file a Form 8-K under Item 1.05 within four business days of determining an intrusion is material
[11].
This strict timeline forces legal, financial, and technical executives to coordinate materiality assessments instantly. Organizations must describe the "material aspects of the nature, scope, and timing of the incident" in their public filings
[12]. The regulation prohibits companies from delaying these determinations. Boards must act "without undue delay" once technical teams discover unauthorized access
[13].
Disclosures present distinct operational risks. Publishing technical details about an active compromise before engineers fully patch the vulnerability invites copycat attacks. The SEC noted this concern but maintained the four-day deadline to prioritize investor transparency. Companies can only delay their Form 8-K filing if the United States Attorney General officially determines that immediate disclosure poses a substantial risk to national security
[13].
Regulators expect detailed governance reporting alongside these rapid incident notices. Form 10-K filings must now include an annual description of the company's defensive strategies. Boards of directors must explicitly detail how they oversee threat management and which specific executive committees hold responsibility for digital risks
[14].
Technology vendors face intense scrutiny under these rules. The SEC charged SolarWinds and its Chief Information Security Officer with securities fraud in 2024, alleging the company misled shareholders about known vulnerabilities
[14]. The agency also charged Avaya Holdings and Mimecast Limited for failing to update their risk factors following third-party intrusions
[15].
Because software vendors hold the keys to their clients' infrastructure, a breach in their systems triggers cascading reporting requirements across the economy. This liability chain has forced service providers to adopt
cloud security platforms for cybersecurity firms that feature continuous code scanning and automated audit trails. If an internal development environment is compromised, the firm needs exact timestamps to defend its materiality assessment before regulators.
Platform Consolidation and Agent Fatigue
Enterprise buyers no longer want dozens of disconnected security tools. Managing separate software agents for vulnerability scanning, posture management, and log analysis strains server processors and exhausts security teams.
The market responded by merging distinct product categories. The Cloud Access Security Broker and Cloud Workload Protection Platform segments are converging rapidly. Gartner estimates this combined market will generate $8.7 billion in 2025, an increase from $6.7 billion in 2024
[16].
Vendors execute major acquisitions to build these unified suites. Wiz purchased Gem Security for $350 million in April 2024
[2]. The acquisition gave Wiz agentless detection and response capabilities. Rather than relying on periodic system scans, the platform can now analyze network logs in real time to contain active threats faster. Wiz followed this by launching products aimed directly at competitors, introducing application security tools to challenge Snyk and threat detection systems to rival CrowdStrike
[4].
Unified platforms solve critical visibility problems for decentralized organizations. Companies with remote staff often lack visibility into which devices are pulling data from corporate servers. Using integrated
cloud security platforms for contractors allows field managers to enforce access policies on mobile devices without installing heavy software agents that drain battery life or trigger privacy complaints.
Consolidation also reduces vendor management overhead. Procurement departments prefer negotiating one master service agreement rather than managing renewals for fifteen different startups. Google's aggressive $23 billion bid for Wiz highlighted this strategy. The search provider wanted to acquire vulnerability scanning, container protection, and application interface monitoring in a single transaction to compete directly with Microsoft's bundled software offerings
[17].
Artificial Intelligence as an Operational Countermeasure
Malicious actors use generative AI to scale their operations. Attackers deploy large language models to write convincing phishing emails, generate exploit code, and automate the discovery of exposed server buckets. Gartner analysts expect generative AI will play a role in 17% of all cyberattacks by 2027
[16].
Human analysts cannot review network traffic logs fast enough to counter algorithmically generated attacks. Defensive software now relies heavily on machine learning models to identify abnormal behaviors. Sixty-seven percent of organizations deploy AI and automation across their security operations centers
[7].
This automation yields measurable financial returns. Organizations that use AI extensively across their prevention workflows save an average of $2.2 million per data breach
[7]. The technology parses millions of server requests per minute, instantly isolating compromised virtual machines before attackers can move laterally into payment databases or personnel files.
Labor shortages accelerate this shift toward automated defense systems. The cybersecurity industry faces a chronic deficit of qualified engineers. IBM found that 53% of breached organizations reported significant security staff shortages in 2024
[10]. Operating with an understaffed team increases the average cost of a data breach by $1.76 million.
Companies supplement their internal teams by hiring external experts. Spending on security professional services will grow from $27.3 billion in 2024 to $42.3 billion in 2028
[5]. Managed security services spending will experience similar growth, rising from $24.1 billion to $42.1 billion over the same period. Outsourcing incident response allows businesses to access elite analysts precisely when an intrusion occurs.
Digital Sovereignty and Vertical Specialization
Generic computing environments no longer satisfy the strict compliance requirements of heavily regulated industries. Software vendors now build specific platform iterations customized for distinct sectors. Gartner estimates that 50% of enterprises will utilize industry-specific cloud platforms by 2028
[18].
Healthcare networks face the most severe penalties for mishandling records. Privacy laws mandate strict encryption standards for patient data both in transit and at rest. To avoid massive regulatory fines, hospital administrators deploy
cloud security platforms for medical offices that automatically detect and redact protected health information before it leaves the local network.
Geopolitics influence how multinational corporations purchase hosting services. Governments increasingly demand that their citizens' data remain within national borders. Digital sovereignty now dictates cloud architecture. By 2027, 70% of enterprises will list digital sovereignty and sustainability as their primary criteria when selecting generative AI services
[19].
Organizations cannot run sensitive machine learning algorithms on public servers hosted in foreign jurisdictions. They require sovereign cloud deployments that guarantee localized data processing. This requirement forces security vendors to build monitoring agents that comply with diverse regional privacy laws simultaneously.
Future Outlook for Security Budgets
Executives view network defense as a non-negotiable operational expense. While financial officers cut software budgets in marketing and human resources, cybersecurity spending remains insulated from macroeconomic headwinds. Ninety percent of security and risk management leaders expect their budgets to increase in 2025
[5].
Data privacy investments reflect this reality. Spending on data security applications will grow from $6.1 billion in 2024 to $10.3 billion by 2028, representing a 14.0% compound annual growth rate
[5]. Companies prioritize tools that monitor file permissions and prevent unauthorized downloads.
The transition from physical servers to distributed architecture fundamentally changes how companies assess risk. By 2027, investigations involving third-party infrastructure will account for more than two-thirds of all reported cybersecurity incidents
[20]. Security teams must defend virtual machines they do not own and secure network connections they do not control.
As cloud computing shifts from a disruptive innovation to a standard business requirement, the platforms protecting these assets will dictate corporate survival. Companies that fail to deploy automated threat detection risk financial ruin through regulatory penalties, lost customer trust, and extended operational downtime.