SIEM & Security Analytics Platforms
These are the specialized categories within SIEM & Security Analytics Platforms. Looking for something broader? See all Cybersecurity, Privacy & Compliance Software categories.
LRQA SIEM Services
Best for Security Information & Event Management (SIEM) for Marketing Agencies

LRQA's Security Information and Event Management (SIEM) Services is a next-gen solution tailored for marketing agencies, emphasizing the detection, analysis, and response to security events and threats. It addresses the industry's unique needs by securing sensitive data, enabling compliance and offering unrivalled visibility into potential cybersecurity threats.
Best for Security Information & Event Management (SIEM) for Marketing Agencies
Expert Take
LRQA SIEM Services offers advanced threat detection and compliance support tailored for marketing agencies, making it a top choice in its niche. Its strong market credibility and robust capabilities are supported by industry recognition and comprehensive documentation.
Pros
- Full suite of CREST accreditations
- NCSC CIR Level 2 Assured
- Microsoft Solutions Partner for Security
- Transparent G-Cloud base pricing
- Integrated Threat Intelligence (6.5T signals)
Cons
- Heavy reliance on Microsoft Sentinel
- Ambiguous 'unit' pricing definition
- Manual scoping required for final cost
- Limited user control over integrations
- Complex setup for non-Azure clients
Best for teams that are
- Organizations seeking a fully managed SIEM service with 24/7 SOC monitoring
- Businesses needing CREST-accredited compliance and threat detection expertise
- Companies wanting to outsource security operations rather than build in-house
Skip if
- Teams wanting to purchase and manage their own SIEM software in-house
- Organizations with small budgets not requiring a full managed security service
- Enterprises preferring to keep all security data and operations internal
Best for teams that are
- Organizations seeking a fully managed SIEM service with 24/7 SOC monitoring
- Businesses needing CREST-accredited compliance and threat detection expertise
- Companies wanting to outsource security operations rather than build in-house
Skip if
- Teams wanting to purchase and manage their own SIEM software in-house
- Organizations with small budgets not requiring a full managed security service
- Enterprises preferring to keep all security data and operations internal
Pros
- Full suite of CREST accreditations
- NCSC CIR Level 2 Assured
- Microsoft Solutions Partner for Security
- Transparent G-Cloud base pricing
- Integrated Threat Intelligence (6.5T signals)
Cons
- Heavy reliance on Microsoft Sentinel
- Ambiguous 'unit' pricing definition
- Manual scoping required for final cost
- Limited user control over integrations
- Complex setup for non-Azure clients
Expert Take
LRQA SIEM Services offers advanced threat detection and compliance support tailored for marketing agencies, making it a top choice in its niche. Its strong market credibility and robust capabilities are supported by industry recognition and comprehensive documentation.
CrowdStrike Falcon SIEM
Best for Security Information & Event Management (SIEM) for Digital Marketing Agencies

CrowdStrike Falcon SIEM is designed specifically for digital marketing agencies that need to protect their clients' data and respond to security threats in real-time. Its AI-powered threat detection and response, along with deep visibility into all network events, enable agencies to maintain the utmost data integrity and confidentiality.
Best for Security Information & Event Management (SIEM) for Digital Marketing Agencies
Expert Take
CrowdStrike Falcon SIEM is positioned as a leading solution for digital marketing agencies, offering AI-powered threat detection and real-time response capabilities. Its design caters specifically to the needs of these agencies, ensuring data integrity and security. The product's strong market credibility and comprehensive feature set justify its high scores.
Pros
- 150x faster search speed via index-free architecture
- Scales to over 1 petabyte of daily data ingestion
- Unified agent for EDR, identity, and SIEM data
- Ecosystem supports 500+ ISV data source integrations
- AI-native automation with Charlotte AI integration
Cons
- Steep learning curve for CrowdStrike Query Language (CQL)
- Custom log parsing requires manual tuning
- Premium pricing for heavy log retention
- Reporting customization can be complex for new users
- UI performance can lag under very high query loads
Best for teams that are
- Organizations already consolidated on the CrowdStrike Falcon platform
- Enterprises requiring high-speed search and petabyte-scale log management
- Teams needing unified endpoint, identity, and cloud telemetry
Skip if
- Small businesses seeking a low-cost, standalone log tool
- Organizations not interested in the broader CrowdStrike ecosystem
- Teams needing extensive support for legacy on-premise data sources
Best for teams that are
- Organizations already consolidated on the CrowdStrike Falcon platform
- Enterprises requiring high-speed search and petabyte-scale log management
- Teams needing unified endpoint, identity, and cloud telemetry
Skip if
- Small businesses seeking a low-cost, standalone log tool
- Organizations not interested in the broader CrowdStrike ecosystem
- Teams needing extensive support for legacy on-premise data sources
Pros
- 150x faster search speed via index-free architecture
- Scales to over 1 petabyte of daily data ingestion
- Unified agent for EDR, identity, and SIEM data
- Ecosystem supports 500+ ISV data source integrations
- AI-native automation with Charlotte AI integration
Cons
- Steep learning curve for CrowdStrike Query Language (CQL)
- Custom log parsing requires manual tuning
- Premium pricing for heavy log retention
- Reporting customization can be complex for new users
- UI performance can lag under very high query loads
Expert Take
CrowdStrike Falcon SIEM is positioned as a leading solution for digital marketing agencies, offering AI-powered threat detection and real-time response capabilities. Its design caters specifically to the needs of these agencies, ensuring data integrity and security. The product's strong market credibility and comprehensive feature set justify its high scores.
Imperva SIEM Solution
Best for Security Information & Event Management (SIEM) for Cybersecurity Firms
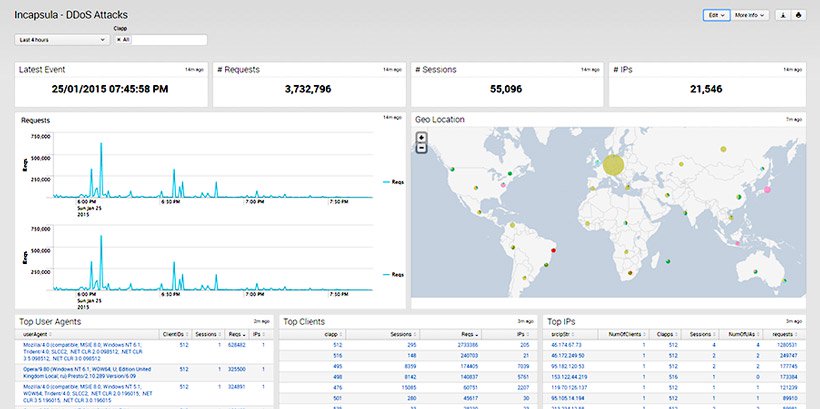
Imperva's Security Information and Event Management (SIEM) Solution offers a comprehensive view of an organization's cybersecurity landscape. Designed specifically for cybersecurity firms, it addresses their need for real-time monitoring, trend analysis, and incident response, thus enabling them to identify and mitigate security threats more effectively.
Best for Security Information & Event Management (SIEM) for Cybersecurity Firms
Expert Take
Imperva SIEM Solution is recognized for its comprehensive capabilities in real-time threat detection and compliance with industry standards, making it a top choice for cybersecurity firms. While the implementation process may be complex, its robust features and scalability justify its premium positioning.
Pros
- Reduces SIEM ingestion costs by ~90%
- AI correlates millions of events into narratives
- Low false positive rate for web threats
- Deep visibility into database activity
- 260+ out-of-the-box integrations
Cons
- Expensive enterprise pricing model
- Steep learning curve for new users
- UI can be laggy and confusing
- Support sometimes relies on documentation
- Not a standalone general IT SIEM
Best for teams that are
- Existing Imperva WAF or Database Security customers
- Teams needing to integrate application attack data into Splunk or Sentinel
- Enterprises requiring granular visibility into web and database threats
Skip if
- Organizations looking for a standalone, general-purpose SIEM
- Non-Imperva customers as it requires Imperva products to function
- Small businesses without an existing primary SIEM platform
Best for teams that are
- Existing Imperva WAF or Database Security customers
- Teams needing to integrate application attack data into Splunk or Sentinel
- Enterprises requiring granular visibility into web and database threats
Skip if
- Organizations looking for a standalone, general-purpose SIEM
- Non-Imperva customers as it requires Imperva products to function
- Small businesses without an existing primary SIEM platform
Pros
- Reduces SIEM ingestion costs by ~90%
- AI correlates millions of events into narratives
- Low false positive rate for web threats
- Deep visibility into database activity
- 260+ out-of-the-box integrations
Cons
- Expensive enterprise pricing model
- Steep learning curve for new users
- UI can be laggy and confusing
- Support sometimes relies on documentation
- Not a standalone general IT SIEM
Expert Take
Imperva SIEM Solution is recognized for its comprehensive capabilities in real-time threat detection and compliance with industry standards, making it a top choice for cybersecurity firms. While the implementation process may be complex, its robust features and scalability justify its premium positioning.
Securonix SIEM Solution
Best for Security Information & Event Management (SIEM) for Contractors

Securonix SIEM Solution is a specifically designed system for contractors seeking to improve their cybersecurity measures. It is capable of ingesting all data across the enterprise, normalizing it to make it more understandable, and then applying analytics and threat detection algorithms to identify potential risks. It fills the industry's need for a robust, comprehensive, and efficient cybersecurity tool.
Best for Security Information & Event Management (SIEM) for Contractors
Expert Take
Securonix SIEM Solution is recognized for its comprehensive data ingestion, advanced analytics, and customizable threat detection, making it a top choice for contractors in the cybersecurity sector. Its market credibility is reinforced by industry certifications and partnerships, while its usability is supported by an intuitive interface and 24/7 support.
Pros
- Built on Snowflake for massive scalability
- 365 days of 'Hot' searchable data
- Pioneering UEBA and behavioral analytics
- 6-time Gartner Magic Quadrant Leader
- AI-Reinforced threat detection (Agentic AI)
Cons
- High starting price (approx. $67k/year)
- Support response times can be slow
- Custom data parsing is complex
- Report generation performance issues
- Steep learning curve for advanced features
Best for teams that are
- Large enterprises dealing with massive data volumes and complex insider threats
- Organizations prioritizing advanced User and Entity Behavior Analytics (UEBA)
- Security teams needing a scalable solution built on Snowflake Data Cloud
Skip if
- Small businesses with simple logging and compliance requirements
- Organizations with low security maturity looking for basic tools
- Teams with small budgets unable to support an enterprise-grade analytics platform
Best for teams that are
- Large enterprises dealing with massive data volumes and complex insider threats
- Organizations prioritizing advanced User and Entity Behavior Analytics (UEBA)
- Security teams needing a scalable solution built on Snowflake Data Cloud
Skip if
- Small businesses with simple logging and compliance requirements
- Organizations with low security maturity looking for basic tools
- Teams with small budgets unable to support an enterprise-grade analytics platform
Pros
- Built on Snowflake for massive scalability
- 365 days of 'Hot' searchable data
- Pioneering UEBA and behavioral analytics
- 6-time Gartner Magic Quadrant Leader
- AI-Reinforced threat detection (Agentic AI)
Cons
- High starting price (approx. $67k/year)
- Support response times can be slow
- Custom data parsing is complex
- Report generation performance issues
- Steep learning curve for advanced features
Expert Take
Securonix SIEM Solution is recognized for its comprehensive data ingestion, advanced analytics, and customizable threat detection, making it a top choice for contractors in the cybersecurity sector. Its market credibility is reinforced by industry certifications and partnerships, while its usability is supported by an intuitive interface and 24/7 support.
Bridewell Managed SIEM
Best for Security Information & Event Management (SIEM) for Marketing Agencies

Bridewell's Managed SIEM is tailored for marketing agencies, providing real-time visibility into threats and anomalies. It supports incident response and forensics, crucial for data-driven sectors like marketing where data security is paramount.
Best for Security Information & Event Management (SIEM) for Marketing Agencies
Expert Take
Bridewell Managed SIEM is a specialized solution for marketing agencies, offering robust capabilities in threat detection and incident response. Its market credibility is supported by third-party recognitions, and it provides a strong user experience with 24/7 support. However, its enterprise pricing may limit accessibility for smaller agencies.
Pros
- NCSC Assured & CREST Accredited
- Specialized in Critical National Infrastructure
- Proprietary Cybiquity Defend portal
- 24/7 UK-based Security Operations Centre
- Rapid "Deployment as Code" methodology
Cons
- Potential SaaS API integration limitations
- Deployment costs charged separately
- Heavily centered on Microsoft Sentinel
- Variable pricing based on scope
Best for teams that are
- Highly regulated sectors like critical infrastructure needing 24/7 managed detection
- Organizations adopting Microsoft Sentinel but lacking in-house SOC staff
- Enterprises requiring a hybrid or co-managed SOC model
Skip if
- Companies seeking a standalone software license to manage themselves
- Small businesses with low security maturity not needing enterprise services
- Organizations not interested in using Microsoft Sentinel as the underlying tech
Best for teams that are
- Highly regulated sectors like critical infrastructure needing 24/7 managed detection
- Organizations adopting Microsoft Sentinel but lacking in-house SOC staff
- Enterprises requiring a hybrid or co-managed SOC model
Skip if
- Companies seeking a standalone software license to manage themselves
- Small businesses with low security maturity not needing enterprise services
- Organizations not interested in using Microsoft Sentinel as the underlying tech
Pros
- NCSC Assured & CREST Accredited
- Specialized in Critical National Infrastructure
- Proprietary Cybiquity Defend portal
- 24/7 UK-based Security Operations Centre
- Rapid "Deployment as Code" methodology
Cons
- Potential SaaS API integration limitations
- Deployment costs charged separately
- Heavily centered on Microsoft Sentinel
- Variable pricing based on scope
Expert Take
Bridewell Managed SIEM is a specialized solution for marketing agencies, offering robust capabilities in threat detection and incident response. Its market credibility is supported by third-party recognitions, and it provides a strong user experience with 24/7 support. However, its enterprise pricing may limit accessibility for smaller agencies.
Deloitte SIEM Technology
Best for Security Information & Event Management (SIEM) for Accountants

Deloitte's Security Information and Event Management (SIEM) Technology is a powerful tool specifically designed for accountants to detect and respond to security threats promptly. The software addresses the industry's need for robust cybersecurity measures and compliance with privacy laws while managing vast amounts of sensitive financial data.
Best for Security Information & Event Management (SIEM) for Accountants
Expert Take
Deloitte SIEM Technology is tailored for the financial sector, offering advanced threat detection and compliance support. Its market credibility is reinforced by Deloitte's established reputation in cybersecurity. While pricing transparency is limited, the product's depth and usability for accountants handling sensitive data justify its premium positioning.
Pros
- Tailored for financial sector
- Advanced threat detection
- Compliance support
- In-depth security insights
Cons
- No clear pricing structure
- May be complex for beginners
Best for teams that are
- Large organizations looking to outsource security operations via a Managed Service (MXDR)
- Enterprises with complex regulatory requirements needing expert consulting and risk advisory
- Companies wanting 24/7 threat monitoring without hiring and training internal SOC staff
Skip if
- IT teams looking to purchase and manage their own standalone SIEM software license
- Small businesses with low budgets unable to afford premium managed consulting services
- Organizations that prefer keeping all security data and operations strictly in-house
Best for teams that are
- Large organizations looking to outsource security operations via a Managed Service (MXDR)
- Enterprises with complex regulatory requirements needing expert consulting and risk advisory
- Companies wanting 24/7 threat monitoring without hiring and training internal SOC staff
Skip if
- IT teams looking to purchase and manage their own standalone SIEM software license
- Small businesses with low budgets unable to afford premium managed consulting services
- Organizations that prefer keeping all security data and operations strictly in-house
Pros
- Tailored for financial sector
- Advanced threat detection
- Compliance support
- In-depth security insights
Cons
- No clear pricing structure
- May be complex for beginners
Expert Take
Deloitte SIEM Technology is tailored for the financial sector, offering advanced threat detection and compliance support. Its market credibility is reinforced by Deloitte's established reputation in cybersecurity. While pricing transparency is limited, the product's depth and usability for accountants handling sensitive data justify its premium positioning.
Rapid7 SIEM Solution
Best for Security Information & Event Management (SIEM) for Marketing Agencies

Rapid7's SIEM solution is specifically tailored for marketing agencies needing to handle large volumes of security data. With its ability to collect, correlate, and analyze security data in real-time, it provides comprehensive visibility, threat detection, and response, ensuring the safety of sensitive marketing data.
Best for Security Information & Event Management (SIEM) for Marketing Agencies
Expert Take
Rapid7's SIEM solution is highly regarded for its real-time data analysis and comprehensive threat detection capabilities, particularly tailored for marketing agencies. Its strong market credibility and usability make it a top choice, despite the need for technical expertise and a higher price point.
Pros
- Deploys in days, not months
- Includes UBA and deception technology
- 8,000+ curated detection rules
- Transparent asset-based pricing
- Cloud-native SaaS architecture
Cons
- Minimum 500 asset purchase required
- Less customizable than legacy SIEMs
- Dashboard lag under high load
- ITSM API integrations can be complex
- Data retention costs for long-term
Best for teams that are
- Mid-sized to large enterprises seeking an easy-to-deploy cloud SIEM
- Teams prioritizing User and Entity Behavior Analytics (UEBA) for detection
- Organizations wanting a high-visibility tool with minimal maintenance overhead
Skip if
- Organizations requiring deep customization of correlation rules like legacy SIEMs
- Businesses mandating strict on-premise data storage without cloud connectivity
- Teams needing a highly complex, programmable correlation engine
Best for teams that are
- Mid-sized to large enterprises seeking an easy-to-deploy cloud SIEM
- Teams prioritizing User and Entity Behavior Analytics (UEBA) for detection
- Organizations wanting a high-visibility tool with minimal maintenance overhead
Skip if
- Organizations requiring deep customization of correlation rules like legacy SIEMs
- Businesses mandating strict on-premise data storage without cloud connectivity
- Teams needing a highly complex, programmable correlation engine
Pros
- Deploys in days, not months
- Includes UBA and deception technology
- 8,000+ curated detection rules
- Transparent asset-based pricing
- Cloud-native SaaS architecture
Cons
- Minimum 500 asset purchase required
- Less customizable than legacy SIEMs
- Dashboard lag under high load
- ITSM API integrations can be complex
- Data retention costs for long-term
Expert Take
Rapid7's SIEM solution is highly regarded for its real-time data analysis and comprehensive threat detection capabilities, particularly tailored for marketing agencies. Its strong market credibility and usability make it a top choice, despite the need for technical expertise and a higher price point.
Secuinfra SIEM Solution
Best for Security Information & Event Management (SIEM) for Insurance Agents

Secuinfra's SIEM solution is a sophisticated cybersecurity tool specifically tailored for the insurance industry. It provides comprehensive and real-time analysis of security alerts generated by applications and network hardware. This solution effectively addresses the industry's need for advanced protection against cyber threats, given the vast amount of sensitive data insurance agents handle.
Best for Security Information & Event Management (SIEM) for Insurance Agents
Expert Take
Secuinfra SIEM Solution stands out in the cybersecurity domain for the insurance industry with its tailored threat detection and real-time monitoring capabilities. Despite the complex setup, its comprehensive log analysis and industry-specific focus justify its premium positioning.
Pros
- Proprietary MITRE ATT&CK use case library
- Client retains ownership of SIEM content
- Data stays in customer network (Co-Managed)
- ISO 27001 certified German provider
- Supports Splunk, ArcSight, and Sentinel
Cons
- Initial onboarding guidance needs improvement
- Proactivity on infrastructure maintenance could be better
- Pricing requires consultation (not public)
- Primary focus on DACH region
Best for teams that are
- Companies needing expert consulting for Splunk/Sentinel
- Organizations requiring co-managed SOC services
- Enterprises in the DACH region needing local support
Skip if
- Buyers looking to purchase standalone software licenses
- Small businesses outside the service region
- Teams wanting a plug-and-play SaaS tool without service
Best for teams that are
- Companies needing expert consulting for Splunk/Sentinel
- Organizations requiring co-managed SOC services
- Enterprises in the DACH region needing local support
Skip if
- Buyers looking to purchase standalone software licenses
- Small businesses outside the service region
- Teams wanting a plug-and-play SaaS tool without service
Pros
- Proprietary MITRE ATT&CK use case library
- Client retains ownership of SIEM content
- Data stays in customer network (Co-Managed)
- ISO 27001 certified German provider
- Supports Splunk, ArcSight, and Sentinel
Cons
- Initial onboarding guidance needs improvement
- Proactivity on infrastructure maintenance could be better
- Pricing requires consultation (not public)
- Primary focus on DACH region
Expert Take
Secuinfra SIEM Solution stands out in the cybersecurity domain for the insurance industry with its tailored threat detection and real-time monitoring capabilities. Despite the complex setup, its comprehensive log analysis and industry-specific focus justify its premium positioning.
Emerson's SIEM Solution
Best for Security Information & Event Management (SIEM) for Contractors

Emerson's SIEM is a cybersecurity tool designed specifically for contractors in need of advanced, consistent monitoring for their control system layer. It provides correlated access to security events, ensuring any potential threats are identified and dealt with promptly, thus minimizing potential damage to the system.
Best for Security Information & Event Management (SIEM) for Contractors
Expert Take
Emerson's SIEM Solution is tailored for contractors, offering advanced monitoring and threat detection capabilities specifically for control systems. Its focus on securing critical infrastructure and providing real-time event correlation makes it a top choice in its category. While pricing and integration complexity may be considerations, its specialized features and industry relevance justify its premium positioning.
Pros
- Deep integration with DeltaV DCS
- ISASecure SSA Level 1 certified
- Real-time OT threat correlation
- Seamless SOC and IT integration
- Automated compliance reporting tools
Cons
- Limited to 500 EPS (virtual)
- Requires certified professional for install
- Physical hardware requires separate purchase
- Max 50 data sources (virtual)
- Opaque custom pricing model
Best for teams that are
- Industrial facilities using Emerson's DeltaV distributed control systems
- OT environments requiring specialized monitoring separate from IT SIEMs
- Plants needing to bridge the gap between IT security and OT operational data
Skip if
- Standard corporate IT environments without industrial control systems
- Organizations not using Emerson DeltaV automation technology
- Small businesses looking for general office network security
Best for teams that are
- Industrial facilities using Emerson's DeltaV distributed control systems
- OT environments requiring specialized monitoring separate from IT SIEMs
- Plants needing to bridge the gap between IT security and OT operational data
Skip if
- Standard corporate IT environments without industrial control systems
- Organizations not using Emerson DeltaV automation technology
- Small businesses looking for general office network security
Pros
- Deep integration with DeltaV DCS
- ISASecure SSA Level 1 certified
- Real-time OT threat correlation
- Seamless SOC and IT integration
- Automated compliance reporting tools
Cons
- Limited to 500 EPS (virtual)
- Requires certified professional for install
- Physical hardware requires separate purchase
- Max 50 data sources (virtual)
- Opaque custom pricing model
Expert Take
Emerson's SIEM Solution is tailored for contractors, offering advanced monitoring and threat detection capabilities specifically for control systems. Its focus on securing critical infrastructure and providing real-time event correlation makes it a top choice in its category. While pricing and integration complexity may be considerations, its specialized features and industry relevance justify its premium positioning.
MPGSOC Managed SIEM
Best for Security Information & Event Management (SIEM) for Digital Marketing Agencies

MPGSOC's Managed SIEM offers digital marketing agencies a tailored approach to security, providing detailed visibility into the complex risk landscape. Its proactive monitoring and threat detection capabilities ensure the security of digital assets, customer data, and intellectual property, which are crucial to the marketing industry.
Best for Security Information & Event Management (SIEM) for Digital Marketing Agencies
Expert Take
MPGSOC Managed SIEM is tailored for digital marketing agencies, offering industry-specific security solutions with proactive threat detection and 24/7 support. Its focus on protecting digital assets and customer data aligns with the needs of marketing agencies, positioning it as a top choice in its niche.
Pros
- FedRAMP 3PAO accredited provider
- Bundled Sumo Logic software licensing
- 24/7 certified security experts
- Designated Customer Success Manager
- Supports multi-cloud environments
Cons
- Pricing requires sales consultation
- Core bundle tied to Sumo Logic
- Full remediation requires SOCaaS upgrade
- No free trial advertised
Best for teams that are
- US Federal agencies and government contractors requiring FedRAMP compliance
- Organizations needing a managed service wrapping CrowdStrike or Sumo Logic
- Entities requiring 24/7 monitoring by US-based analysts
Skip if
- Small businesses looking for a simple, self-managed software tool
- Companies outside regulated sectors seeking low-cost generic logging
- Organizations wanting to manage their own SIEM infrastructure
Best for teams that are
- US Federal agencies and government contractors requiring FedRAMP compliance
- Organizations needing a managed service wrapping CrowdStrike or Sumo Logic
- Entities requiring 24/7 monitoring by US-based analysts
Skip if
- Small businesses looking for a simple, self-managed software tool
- Companies outside regulated sectors seeking low-cost generic logging
- Organizations wanting to manage their own SIEM infrastructure
Pros
- FedRAMP 3PAO accredited provider
- Bundled Sumo Logic software licensing
- 24/7 certified security experts
- Designated Customer Success Manager
- Supports multi-cloud environments
Cons
- Pricing requires sales consultation
- Core bundle tied to Sumo Logic
- Full remediation requires SOCaaS upgrade
- No free trial advertised
Expert Take
MPGSOC Managed SIEM is tailored for digital marketing agencies, offering industry-specific security solutions with proactive threat detection and 24/7 support. Its focus on protecting digital assets and customer data aligns with the needs of marketing agencies, positioning it as a top choice in its niche.
Explore Categories
- Security Information & Event Management (SIEM) for Accountants
- Security Information & Event Management (SIEM) for Contractors
- Security Information & Event Management (SIEM) for Cybersecurity Firms
- Security Information & Event Management (SIEM) for Digital Marketing Agencies
- Security Information & Event Management (SIEM) for Insurance Agents
- Security Information & Event Management (SIEM) for Marketing Agencies