
Recent industry data from 2024 and early 2025 reveals a critical qualitative shift in the Single Sign-On (SSO) landscape: while overall SSO adoption continues to grow, there is a distinct migration away from low-assurance factors (like SMS) toward phishing-resistant authenticators (such as FIDO2/WebAuthn and Okta FastPass). This trend is driven by the escalating success of Adversary-in-the-Middle (AiTM) attacks that easily bypass traditional MFA, forcing enterprises to upgrade their SSO infrastructure from simple connectivity tools to genuine Zero Trust enablers. The data h
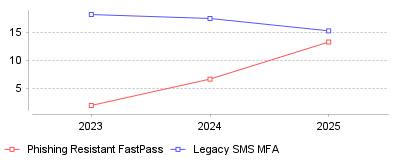
| Year | Phishing Resistant FastPass | Legacy SMS MFA |
|---|---|---|
| 2023 | 2.0 | 18.2 |
| 2024 | 6.7 | 17.5 |
| 2025 | 13.3 | 15.3 |
The data illustrates a rapid aggressive divergence in authenticator preference within Single Sign-On (SSO) environments over the last three years. Specifically, the adoption of phishing-resistant methods, such as Okta FastPass and FIDO2/WebAuthn, has nearly doubled year-over-year, rising from approximately 6.7% in early 2024 to 13.3% in early 2025 [1]. Concurrently, reliance on low-assurance factors like SMS for Multi-Factor Authentication (MFA) has begun a measurable decline, dropping to 15.3% as organizations retire vulnerable credentials in favor of cryptographic proof [1].
This trend signifies a maturity milestone in the Identity and Access Management (IAM) industry: the "deploy MFA everywhere" phase is ending, replaced by "deploy the right MFA." For the micro-industry, SSO providers are no longer just selling convenient access; they are becoming the primary defense against sophisticated credential theft, integrating biometric and device-bound keys directly into the login flow. On a macro level, this shift indicates that enterprises are reacting to the commoditization of phishing kits; attackers can now easily bypass SMS OTPs, rendering standard SSO setups vulnerable without phishing-resistant layers [2]. The growth of passwordless standards like WebAuthn suggests that the long-promised "passwordless future" is finally achieving statistical significance in workforce environments.
This transition is critical because traditional SSO implementations created a single point of failure: if an attacker bypassed the primary authentication (often via a phished password and OTP), they gained access to the entire enterprise suite. Recent data shows that while 63% of accounts use some form of MFA, barely 1% of SSO accounts were using phishing-resistant methods prior to this recent surge, leaving vast attack surfaces exposed to Adversary-in-the-Middle (AiTM) attacks [2]. The sharp rise in high-assurance adoption (up 63% collectively for phishing-resistant methods) demonstrates that organizations are prioritizing resilience over mere compliance [1].
The primary catalyst is likely the prevalence of "MFA fatigue" attacks and advanced phishing toolkits (like Evilginx) that proxy real-time login pages to steal session tokens, making SMS and push notifications ineffective [3]. Furthermore, strict regulatory guidance from bodies like CISA and the move toward Zero Trust architectures have pressured CISOs to eliminate "phishable" factors [4]. Additionally, the improved usability of platform authenticators (TouchID, Windows Hello) has lowered the friction for users, disproving the old axiom that higher security equals a poorer user experience [1].
The data confirms that the SSO market is bifurcating: legacy implementations relying on passwords and SMS are fading, while cryptographic, passwordless logins are entering the mainstream. For buyers and administrators, the key takeaway is that an SSO solution without integrated phishing-resistant MFA is increasingly viewed as a liability rather than an asset. Organizations should audit their current authenticator mix and accelerate the deprecation of SMS and OTPs to close the gap against modern identity threats.
The operational landscape of digital identity has shifted fundamentally. Once viewed primarily as a productivity tool to reduce password fatigue, Single Sign-On (SSO) has evolved into the primary security perimeter for modern enterprises. As organizations decouple from on-premise infrastructure in favor of cloud-native environments, the centralized management of user identities has become the linchpin of cybersecurity, compliance, and operational efficiency. The market reflects this prioritization: the global SSO market was valued at approximately USD 2.51 billion in 2024 and is projected to expand at a Compound Annual Growth Rate (CAGR) of 13.2% through 2033 [1], [1].
However, this rapid adoption conceals significant operational fractures. Security leaders are currently grappling with the "SSO Tax" that creates barriers for small-to-medium businesses (SMBs), the emergence of "ghost logins" that bypass security protocols, and sophisticated threat actors like Scattered Spider that specifically target identity infrastructure. This report analyzes the current trends, technical challenges, and sector-specific implications of deploying Single Sign-On (SSO) Solutions within the broader context of Cybersecurity, Privacy & Compliance Software.
While the theoretical benefits of SSO—enhanced user experience and centralized control—are well-documented, the operational reality involves complex integration hurdles and economic barriers.

A critical trend in the SaaS market is the gating of SSO capabilities behind "Enterprise" pricing tiers. This phenomenon, often referred to as the "SSO Tax," forces organizations to purchase expensive premium bundles to access basic security features like SAML (Security Assertion Markup Language) or OIDC (OpenID Connect) integration. Research by CISA indicates that this pricing model is a primary barrier for SMBs, leading many to opt for less secure, manual password management methods [2], [3].
The operational implication is a bifurcation of security hygiene. Large enterprises can afford the premium tiers requisite for centralized identity management, while smaller organizations remain vulnerable to credential stuffing and phishing attacks because they cannot justify a 2x or 3x price increase solely for SSO functionality [4], [5]. CISA and other security bodies are increasingly advocating for "Secure by Design" principles where SSO is a standard feature rather than a luxury add-on, arguing that security should not be treated as a premium commodity [6].
Despite the maturity of protocols like SAML 2.0 and OIDC, implementation remains a significant drain on engineering resources. Developers frequently underestimate the complexity of integrating with disparate Identity Providers (IdPs) like Okta, Microsoft Entra ID (formerly Azure AD), and Google Workspace. The lack of strict standardization in how IdPs handle attributes, XML namespaces (in SAML), and token claims (in OIDC) leads to brittle integrations that require constant maintenance [7], [7].
For SaaS vendors, this results in extended sales cycles and high support costs. An integration that works seamlessly for one enterprise client may fail for another due to minor configuration differences in their IdP. This "integration fatigue" drives the adoption of middleware solutions but remains a core operational bottleneck [7].
Centralizing authentication creates a high-value target for threat actors. If an attacker compromises an SSO provider or a privileged admin account, they gain lateral access across the organization’s entire SaaS stack. Current threat intelligence highlights two emerging risks: Ghost Logins and Help Desk social engineering.
A "ghost login" occurs when an application supports SSO but retains a local username/password entry point that is not disabled. Research indicates that approximately 10% of enterprise identities allow both SSO and password authentication simultaneously [8], [8]. This dual-access vulnerability undermines the security promises of SSO; while the front door (SSO) may be guarded by Multi-Factor Authentication (MFA) and conditional access policies, the back door (local password) often remains vulnerable to brute-force attacks or credential stuffing [9].
This issue is exacerbated by "Shadow IT" and "SaaS Sprawl," where employees sign up for applications using corporate emails before an official enterprise agreement is in place. When IT eventually integrates these apps into the corporate SSO, the original local credentials often remain active and unmonitored [10].
The threat landscape has evolved from technical exploitation to psychological manipulation. The cybercriminal group "Scattered Spider" has demonstrated high proficiency in compromising identity systems by targeting IT help desks. By impersonating employees and claiming they have lost their MFA token or phone, these attackers convince help desk agents to reset credentials, effectively bypassing technical controls [11], [12].
Once inside, these actors often establish persistence by registering their own MFA devices. This trend highlights a critical operational gap: identity verification processes at the help desk level are often weaker than the cryptographic controls of the software itself. The shift has forced organizations to reconsider "phishable" MFA methods (like SMS or push notifications) in favor of FIDO2 hardware keys and passkeys [13].
The operational requirements for identity management vary drastically across industries. Regulatory pressure, workforce composition, and data sensitivity dictate different architectural approaches.
Accounting firms are prime targets for cybercriminals due to the volume of sensitive financial and personal data they possess. The operational challenge here is balancing client accessibility with rigorous security. The rise of "Zero Trust" architecture is particularly relevant for CPA firms, which must verify every access request regardless of origin [14].
For these firms, the integration of SSO is not just about employee access but also securing client portals. Phishing attacks targeting tax professionals have risen significantly, necessitating solutions that enforce strict MFA policies. Firms evaluating Single Sign-On (SSO) Solutions for Accountants must prioritize platforms that offer granular audit logs and integration with tax software ecosystems to prevent data exfiltration and maintain client trust during high-pressure tax seasons [15], [16].
The insurance sector faces stringent regulatory mandates, specifically the New York Department of Financial Services (NY DFS) Cybersecurity Regulation (23 NYCRR Part 500). This regulation explicitly requires the use of Multi-Factor Authentication for any individual accessing internal networks from an external network [17]. Crucially, regulatory guidance clarifies that SSO alone does not satisfy this requirement; MFA must be enforced at the IdP level [17], [17].
Furthermore, threat intelligence suggests that groups like Scattered Spider have pivoted from retail to targeting insurance carriers, aiming to exploit the vast repositories of policyholder data [18], [19]. Consequently, Single Sign-On (SSO) Solutions for Insurance Agents must support "phishing-resistant" authentication methods and provide seamless compliance reporting to satisfy state and federal audits [20].
Marketing agencies present a unique operational challenge: "SaaS Sprawl." Agencies often utilize hundreds of distinct tools—from social media schedulers to analytics platforms—many of which do not support enterprise-grade SSO standards like SAML in their lower pricing tiers. Additionally, agencies frequently rely on a fluid workforce of freelancers who require temporary access to client accounts.
The operational risk here is credential sharing. Without centralized identity management, teams often share passwords for platforms like Meta Business Suite or Google Ads via spreadsheets or chat apps. Solutions tailored for this space must handle "non-standard" apps that lack native SSO support, often through secure browser extensions or password vaulting features. Implementing specialized Single Sign-On (SSO) Solutions for Marketing Agencies can mitigate the risk of freelancer offboarding, ensuring that access is revoked immediately upon project completion without needing to change shared passwords manually [21].
Managing the identity lifecycle of temporary workers is a major source of "access creep." Unlike full-time employees, contractors often need access to a limited subset of applications for a defined period. A common failure mode occurs when contractors are offboarded from HR systems but their access to third-party SaaS applications remains active because the systems are not integrated [22].
Automated provisioning and de-provisioning are critical features for this demographic. Organizations deploying Single Sign-On (SSO) Solutions for Contractors should focus on Identity Governance and Administration (IGA) capabilities that enforce time-bound access policies. This ensures that a contractor's digital identity expires automatically, reducing the attack surface related to dormant accounts [23], [24], [25].
The future of SSO lies in the total elimination of the password. The industry is rapidly moving toward passwordless authentication standards, primarily FIDO2 and WebAuthn (Passkeys). By 2025 and beyond, reliance on shared secrets (passwords) will be viewed as a legacy vulnerability [26], [27].
Single Sign-On has graduated from an IT convenience to a critical business continuity asset. However, the implementation of SSO is fraught with challenges ranging from the "SSO Tax" affecting SMBs to the complex lifecycle management of contractors and the persistent threat of social engineering. Organizations must view SSO not as a "set and forget" tool, but as an active ecosystem requiring rigorous configuration, regular auditing for ghost logins, and adaptation to sector-specific compliance mandates. The transition to passwordless architectures represents the next frontier, promising to resolve many of the current vulnerabilities inherent in credential-based access.