Endpoint Security Platforms
These are the specialized categories within Endpoint Security Platforms. Looking for something broader? See all Cybersecurity, Privacy & Compliance Software categories.
Trend Vision One™ Endpoint Security

Trend Vision One™ Endpoint Security is a comprehensive SaaS solution designed for marketing agencies that require robust protection for their diverse digital environments, including servers, IoT devices, and legacy systems. It simplifies the management of cybersecurity, ensuring all endpoints are secure, reducing the risk of data breaches and enhancing client trust.
Best for Endpoint Security Platforms for Marketing Agencies
Expert Take
Trend Vision One™ Endpoint Security is a comprehensive solution tailored for marketing agencies, offering robust protection across diverse digital environments. Its AI-driven capabilities and broad endpoint coverage enhance security management, making it a leading choice in its category.
Pros
- 100% detection rate in MITRE evaluations
- Virtual patching shields unpatched vulnerabilities
- 19 consecutive years as Gartner Leader
- Backed by Zero-Day Initiative bug bounty
- Unified XDR across endpoint and cloud
Cons
- High resource usage on some endpoints
- Steep learning curve for configuration
- Complex credit-based licensing model
- Integration challenges with some third-party tools
- Alert tuning required to reduce noise
Best for teams that are
- Agencies wanting unified endpoint, email, and cloud security
- Organizations needing flexible credit-based licensing
- Teams prioritizing XDR capabilities across hybrid environments
Skip if
- Small businesses wanting simple per-user pricing
- Users who find complex cloud consoles overwhelming
- Companies needing only basic standalone antivirus
Best for teams that are
- Agencies wanting unified endpoint, email, and cloud security
- Organizations needing flexible credit-based licensing
- Teams prioritizing XDR capabilities across hybrid environments
Skip if
- Small businesses wanting simple per-user pricing
- Users who find complex cloud consoles overwhelming
- Companies needing only basic standalone antivirus
Pros
- 100% detection rate in MITRE evaluations
- Virtual patching shields unpatched vulnerabilities
- 19 consecutive years as Gartner Leader
- Backed by Zero-Day Initiative bug bounty
- Unified XDR across endpoint and cloud
Cons
- High resource usage on some endpoints
- Steep learning curve for configuration
- Complex credit-based licensing model
- Integration challenges with some third-party tools
- Alert tuning required to reduce noise
Expert Take
Trend Vision One™ Endpoint Security is a comprehensive solution tailored for marketing agencies, offering robust protection across diverse digital environments. Its AI-driven capabilities and broad endpoint coverage enhance security management, making it a leading choice in its category.

Island Enterprise Browser is a SaaS solution tailor-made for contractors seeking robust endpoint security. It delivers secure, seamless application access, thwarts phishing attempts, malware, and data leakage, and efficiently onboards third-party contractors. This software uniquely addresses the security vulnerabilities that contractors often face, providing robust protection against cyber threats.
Best for Endpoint Security Platforms for Contractors
Expert Take
Island Enterprise Browser excels in providing robust endpoint security tailored for contractors, with strong capabilities in preventing phishing, malware, and data leakage. Its seamless integration and onboarding process for third-party contractors make it a standout in its category. However, limited pricing transparency and potential technical complexity slightly impact its overall usability score.
Pros
- Granular last-mile data controls
- Built-in Robotic Process Automation (RPA)
- Replaces costly VDI infrastructure
- Familiar Chromium-based user interface
- ISO 27001 and SOC 2 certified
Cons
- High minimum entry cost
- Noticeable browser lag reported
- Compatibility issues with legacy apps
- Opaque pricing model
- Password import friction
Best for teams that are
- Organizations securing contractors and BYOD users
- Companies wanting to replace expensive VDI infrastructure
- Teams needing to secure SaaS apps without device agents
Skip if
- General endpoint protection against OS-level malware
- Users needing to secure non-web desktop applications
Best for teams that are
- Organizations securing contractors and BYOD users
- Companies wanting to replace expensive VDI infrastructure
- Teams needing to secure SaaS apps without device agents
Skip if
- General endpoint protection against OS-level malware
- Users needing to secure non-web desktop applications
Pros
- Granular last-mile data controls
- Built-in Robotic Process Automation (RPA)
- Replaces costly VDI infrastructure
- Familiar Chromium-based user interface
- ISO 27001 and SOC 2 certified
Cons
- High minimum entry cost
- Noticeable browser lag reported
- Compatibility issues with legacy apps
- Opaque pricing model
- Password import friction
Expert Take
Island Enterprise Browser excels in providing robust endpoint security tailored for contractors, with strong capabilities in preventing phishing, malware, and data leakage. Its seamless integration and onboarding process for third-party contractors make it a standout in its category. However, limited pricing transparency and potential technical complexity slightly impact its overall usability score.
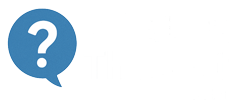
Guardz Endpoint Security is a robust SaaS solution tailored to meet the specific needs of insurance agents. It employs AI and a multilayered approach to ensure the highest levels of data protection and compliance, crucial aspects in the insurance industry.
Best for Endpoint Security Platforms for Insurance Agents
Expert Take
Guardz Endpoint Security excels in providing industry-specific protection for insurance agents, leveraging AI and multilayered security to ensure data protection and compliance. Its market credibility is supported by third-party recognition, and while pricing transparency could be improved, its overall capabilities make it a top choice in its category.
Pros
- Unified dashboard for endpoint, email, and identity
- Free 'Community Shield' plan for MSP internal use
- Includes SentinelOne EDR in Ultimate plan
- Month-to-month billing with no lock-in
- Intuitive 'single pane of glass' interface
Cons
- Native agent relies on Windows Defender
- Linux support requires SentinelOne upgrade
- ITDR features described as basic by users
- Reporting less granular than enterprise tools
- Newer platform with evolving feature set
Best for teams that are
- MSPs and SMBs seeking a unified, easy-to-use platform for endpoint and cloud security
- Organizations wanting managed protection for Microsoft 365 and Google Workspace identities
- Small IT teams needing a cost-effective 'business-in-a-box' security solution
Skip if
- Large enterprises requiring granular, complex policy configurations and custom reporting
- Security teams needing advanced, standalone threat hunting tools without an MSP focus
- Organizations requiring strictly on-premise management without cloud connectivity
Best for teams that are
- MSPs and SMBs seeking a unified, easy-to-use platform for endpoint and cloud security
- Organizations wanting managed protection for Microsoft 365 and Google Workspace identities
- Small IT teams needing a cost-effective 'business-in-a-box' security solution
Skip if
- Large enterprises requiring granular, complex policy configurations and custom reporting
- Security teams needing advanced, standalone threat hunting tools without an MSP focus
- Organizations requiring strictly on-premise management without cloud connectivity
Pros
- Unified dashboard for endpoint, email, and identity
- Free 'Community Shield' plan for MSP internal use
- Includes SentinelOne EDR in Ultimate plan
- Month-to-month billing with no lock-in
- Intuitive 'single pane of glass' interface
Cons
- Native agent relies on Windows Defender
- Linux support requires SentinelOne upgrade
- ITDR features described as basic by users
- Reporting less granular than enterprise tools
- Newer platform with evolving feature set
Expert Take
Guardz Endpoint Security excels in providing industry-specific protection for insurance agents, leveraging AI and multilayered security to ensure data protection and compliance. Its market credibility is supported by third-party recognition, and while pricing transparency could be improved, its overall capabilities make it a top choice in its category.
Harmony Endpoint Protection

Harmony Endpoint is an advanced endpoint security solution, specifically designed to protect remote marketing agencies. Its advanced EPP, EDR and XDR capabilities ensure seamless protection of sensitive data and client information, a vital need in the marketing sector.
Best for Endpoint Security Platforms for Marketing Agencies
Expert Take
Harmony Endpoint Protection excels in providing comprehensive security solutions tailored for marketing agencies, especially those with remote teams. Its advanced threat prevention and incident response capabilities are well-documented, making it a top choice in the endpoint security platform category. While setup complexity may require professional assistance, the overall value and protection offered justify its premium positioning.
Pros
- 100% detection in MITRE ATT&CK
- Unified EPP, EDR, and VPN agent
- Strategic Leader in AV-Comparatives
- Automated ransomware rollback capabilities
- Comprehensive data loss prevention (DLP)
Cons
- High system resource usage reported
- Complex initial setup and configuration
- Difficult uninstallation process
- Unclear pricing transparency
- Steep learning curve for administrators
Best for teams that are
- Remote workforces needing strong anti-ransomware tools
- Agencies requiring unified VPN and endpoint security
- Teams needing automated incident response capabilities
Skip if
- Users with older hardware due to high resource usage
- Teams needing quick deployment without external tools
- Organizations on a tight budget (can be expensive)
Best for teams that are
- Remote workforces needing strong anti-ransomware tools
- Agencies requiring unified VPN and endpoint security
- Teams needing automated incident response capabilities
Skip if
- Users with older hardware due to high resource usage
- Teams needing quick deployment without external tools
- Organizations on a tight budget (can be expensive)
Pros
- 100% detection in MITRE ATT&CK
- Unified EPP, EDR, and VPN agent
- Strategic Leader in AV-Comparatives
- Automated ransomware rollback capabilities
- Comprehensive data loss prevention (DLP)
Cons
- High system resource usage reported
- Complex initial setup and configuration
- Difficult uninstallation process
- Unclear pricing transparency
- Steep learning curve for administrators
Expert Take
Harmony Endpoint Protection excels in providing comprehensive security solutions tailored for marketing agencies, especially those with remote teams. Its advanced threat prevention and incident response capabilities are well-documented, making it a top choice in the endpoint security platform category. While setup complexity may require professional assistance, the overall value and protection offered justify its premium positioning.
Specifically designed for insurance agents, Aurora Endpoint Security offers robust AI-driven threat detection and prevention. It safeguards sensitive client data and ensures compliance with industry-specific cybersecurity regulations, thereby protecting your reputation and business continuity.
Best for Endpoint Security Platforms for Insurance Agents
Expert Take
Aurora Endpoint Security is tailored for insurance agents, offering AI-driven threat detection and compliance with industry regulations. Its focus on protecting sensitive data and maintaining business continuity makes it a strong contender in its niche. The product's 24/7 support and comprehensive security features justify its premium positioning.
Pros
- 100% threat protection in Tolly Group testing
- $3 million Security Operations Warranty included
- 24x7 Managed Detection & Response (MDR)
- Lightweight agent (~33% CPU during scans)
- 100% willingness to recommend on Gartner Peer Insights
Cons
- Granular script control configuration limitations
- Proxy config requires registry edits on Windows
- Notification bugs on macOS Apple Silicon
- Pricing varies significantly by sales channel
- No GUI notifications on Linux endpoints
Best for teams that are
- Organizations seeking a fully managed SOC-as-a-Service rather than just software
- Teams with limited internal security staff needing 24/7 expert monitoring and triage
- Companies wanting to transfer cyber risk through a concierge security model
Skip if
- DIY security teams wanting to purchase and manage a standalone tool themselves
- Companies looking for a low-cost, unmanaged antivirus solution
- Organizations that prefer keeping all security data and logs strictly in-house
Best for teams that are
- Organizations seeking a fully managed SOC-as-a-Service rather than just software
- Teams with limited internal security staff needing 24/7 expert monitoring and triage
- Companies wanting to transfer cyber risk through a concierge security model
Skip if
- DIY security teams wanting to purchase and manage a standalone tool themselves
- Companies looking for a low-cost, unmanaged antivirus solution
- Organizations that prefer keeping all security data and logs strictly in-house
Pros
- 100% threat protection in Tolly Group testing
- $3 million Security Operations Warranty included
- 24x7 Managed Detection & Response (MDR)
- Lightweight agent (~33% CPU during scans)
- 100% willingness to recommend on Gartner Peer Insights
Cons
- Granular script control configuration limitations
- Proxy config requires registry edits on Windows
- Notification bugs on macOS Apple Silicon
- Pricing varies significantly by sales channel
- No GUI notifications on Linux endpoints
Expert Take
Aurora Endpoint Security is tailored for insurance agents, offering AI-driven threat detection and compliance with industry regulations. Its focus on protecting sensitive data and maintaining business continuity makes it a strong contender in its niche. The product's 24/7 support and comprehensive security features justify its premium positioning.
Trellix Endpoint Security
Best for Endpoint Security Platforms for Digital Marketing Agencies

Trellix Endpoint Security is an ideal solution for digital marketing agencies due to its centralized, extensible platform for endpoint security policy management. It addresses the specific need for robust cybersecurity in the industry, enabling agencies to automate daily tasks, protect sensitive data, and maintain the integrity of their digital marketing efforts.
Best for Endpoint Security Platforms for Digital Marketing Agencies
Expert Take
Trellix Endpoint Security excels in providing a centralized and extensible platform tailored for digital marketing agencies. Its advanced threat detection and automation of security tasks support its position as a leading solution in endpoint security. Despite potential complexity for beginners, its robust features and 24/7 support make it a top choice for agencies prioritizing data security.
Pros
- 100% detection rate in SE Labs Q2 2024
- Automated ransomware rollback remediation
- FedRAMP certified centralized management
- Scales to 100,000+ endpoints per appliance
- Integrated Data Loss Prevention (DLP)
Cons
- High CPU/memory usage reported by users
- Steep learning curve for management console
- Complex initial configuration and setup
- Pricing is not publicly transparent
- Support response times can be slow
Best for teams that are
- Large enterprises requiring robust, multi-layered threat prevention [cite: 9]
- Organizations with dedicated security teams to manage complex policies [cite: 10]
Skip if
- Users with older hardware due to high memory and CPU consumption [cite: 10]
- Small IT teams lacking expertise for complex initial setup [cite: 10]
Best for teams that are
- Large enterprises requiring robust, multi-layered threat prevention [cite: 9]
- Organizations with dedicated security teams to manage complex policies [cite: 10]
Skip if
- Users with older hardware due to high memory and CPU consumption [cite: 10]
- Small IT teams lacking expertise for complex initial setup [cite: 10]
Pros
- 100% detection rate in SE Labs Q2 2024
- Automated ransomware rollback remediation
- FedRAMP certified centralized management
- Scales to 100,000+ endpoints per appliance
- Integrated Data Loss Prevention (DLP)
Cons
- High CPU/memory usage reported by users
- Steep learning curve for management console
- Complex initial configuration and setup
- Pricing is not publicly transparent
- Support response times can be slow
Expert Take
Trellix Endpoint Security excels in providing a centralized and extensible platform tailored for digital marketing agencies. Its advanced threat detection and automation of security tasks support its position as a leading solution in endpoint security. Despite potential complexity for beginners, its robust features and 24/7 support make it a top choice for agencies prioritizing data security.
LevelBlue Managed Endpoint Security

LevelBlue Managed Endpoint Security with SentinelOne is specifically designed for the insurance industry to provide comprehensive security for various types of endpoints such as desktops. It offers advanced AI technology to differentiate between harmless and harmful activities, significantly reducing potential risks and enhancing data protection.
Best for Endpoint Security Platforms for Insurance Agents
Expert Take
LevelBlue Managed Endpoint Security excels in providing tailored endpoint security solutions for the insurance industry, leveraging advanced AI technology for risk reduction. Its partnership with SentinelOne enhances its credibility, and the 24/7 support ensures reliability, making it a top choice for insurance agents.
Pros
- Powered by SentinelOne technology
- 24/7 global SOC monitoring
- Unlimited Tenable vulnerability scanning
- Backed by AT&T Cybersecurity heritage
- Integrated Open Threat Exchange (OTX)
Cons
- Pricing is not publicly transparent
- Slower innovation than some competitors
- Support can feel transactional
- Reporting capabilities may be limited
- Complex setup for some features
Best for teams that are
- Companies seeking a fully managed security service (MSSP) with consulting expertise
- Existing AT&T or LevelBlue network customers looking to consolidate vendors
- Organizations needing managed detection and response powered by SentinelOne technology
Skip if
- Teams wanting to purchase and self-manage their own endpoint security software license
- Small businesses looking for a simple, low-cost standalone product
- Organizations that do not require external consulting or managed SOC services
Best for teams that are
- Companies seeking a fully managed security service (MSSP) with consulting expertise
- Existing AT&T or LevelBlue network customers looking to consolidate vendors
- Organizations needing managed detection and response powered by SentinelOne technology
Skip if
- Teams wanting to purchase and self-manage their own endpoint security software license
- Small businesses looking for a simple, low-cost standalone product
- Organizations that do not require external consulting or managed SOC services
Pros
- Powered by SentinelOne technology
- 24/7 global SOC monitoring
- Unlimited Tenable vulnerability scanning
- Backed by AT&T Cybersecurity heritage
- Integrated Open Threat Exchange (OTX)
Cons
- Pricing is not publicly transparent
- Slower innovation than some competitors
- Support can feel transactional
- Reporting capabilities may be limited
- Complex setup for some features
Expert Take
LevelBlue Managed Endpoint Security excels in providing tailored endpoint security solutions for the insurance industry, leveraging advanced AI technology for risk reduction. Its partnership with SentinelOne enhances its credibility, and the 24/7 support ensures reliability, making it a top choice for insurance agents.

Evolvous Endpoint Management is a tailored solution for the construction industry, offering robust endpoint security. It keeps devices secure, boosts productivity, and ensures compliance across multiple job sites and remote teams, addressing the unique needs of construction project management, data security, and remote collaboration.
Best for Endpoint Security Platforms for Contractors
Expert Take
Evolvous Endpoint Management is tailored for the construction industry, providing robust endpoint security and compliance solutions. Its focus on industry-specific needs, such as securing devices across multiple job sites, enhances its credibility as a specialized solution. However, the lack of pricing transparency and potential need for technical proficiency are noted tradeoffs.
Pros
- Verified Microsoft Solutions Partner
- Specialized construction industry focus
- Zero-touch device deployment
- Integrated Zero Trust security
- 50% off Proof of Concept
Cons
- No public pricing schedule
- Intune lacks offline asset tracking
- Heavy Microsoft ecosystem dependency
- Limited third-party reviews
Best for teams that are
- Construction firms managing rugged tablets and field devices
- Companies using Microsoft 365 seeking expert Intune configuration
Skip if
- Businesses seeking a standalone off-the-shelf antivirus product
- Non-construction firms needing generic office security
Best for teams that are
- Construction firms managing rugged tablets and field devices
- Companies using Microsoft 365 seeking expert Intune configuration
Skip if
- Businesses seeking a standalone off-the-shelf antivirus product
- Non-construction firms needing generic office security
Pros
- Verified Microsoft Solutions Partner
- Specialized construction industry focus
- Zero-touch device deployment
- Integrated Zero Trust security
- 50% off Proof of Concept
Cons
- No public pricing schedule
- Intune lacks offline asset tracking
- Heavy Microsoft ecosystem dependency
- Limited third-party reviews
Expert Take
Evolvous Endpoint Management is tailored for the construction industry, providing robust endpoint security and compliance solutions. Its focus on industry-specific needs, such as securing devices across multiple job sites, enhances its credibility as a specialized solution. However, the lack of pricing transparency and potential need for technical proficiency are noted tradeoffs.

Cortex XDR is an AI-powered endpoint security solution specifically designed for contractors. It not only offers robust malware prevention but also detailed threat detection, ensuring full protection for contractors' business operations. Its ability to handle complex security situations, combined with an easy-to-understand interface, makes it an ideal choice for contractors.
Best for Endpoint Security Platforms for Contractors
Expert Take
Cortex XDR Endpoint Security is recognized for its advanced AI-powered threat detection and comprehensive malware prevention, making it a top choice for contractors. It combines robust security features with a user-friendly interface, supported by credible third-party validations and industry-specific capabilities.
Pros
- 100% prevention and detection in MITRE evaluations
- Zero false positives in recent industry tests
- Unified agent for endpoint, network, and cloud
- Granular device control for USB and Bluetooth
- Automated root cause analysis for faster investigations
Cons
- Steep learning curve for new administrators
- Higher price point than many competitors
- Console interface can be complex to navigate
- No on-premises management console available
- Support response times cited as variable
Best for teams that are
- Enterprises with a dedicated Security Operations Center (SOC)
- Existing Palo Alto Networks customers consolidating security
- Teams needing automated response and advanced forensics
Skip if
- Small businesses with limited IT or security staff
- Budget-conscious buyers seeking low-cost protection
Best for teams that are
- Enterprises with a dedicated Security Operations Center (SOC)
- Existing Palo Alto Networks customers consolidating security
- Teams needing automated response and advanced forensics
Skip if
- Small businesses with limited IT or security staff
- Budget-conscious buyers seeking low-cost protection
Pros
- 100% prevention and detection in MITRE evaluations
- Zero false positives in recent industry tests
- Unified agent for endpoint, network, and cloud
- Granular device control for USB and Bluetooth
- Automated root cause analysis for faster investigations
Cons
- Steep learning curve for new administrators
- Higher price point than many competitors
- Console interface can be complex to navigate
- No on-premises management console available
- Support response times cited as variable
Expert Take
Cortex XDR Endpoint Security is recognized for its advanced AI-powered threat detection and comprehensive malware prevention, making it a top choice for contractors. It combines robust security features with a user-friendly interface, supported by credible third-party validations and industry-specific capabilities.
Sophos Endpoint Security
Best for Endpoint Security Platforms for Digital Marketing Agencies

Sophos Endpoint Security offers AI-powered protection specifically designed to combat advanced cyber threats that digital marketing agencies often face. It boasts powerful detection and response tools (EDR/XDR), effectively preventing attacks before they impact your systems, which is crucial in an industry that handles sensitive customer data.
Best for Endpoint Security Platforms for Digital Marketing Agencies
Expert Take
Sophos Endpoint Security is recognized for its advanced AI-powered protection and tailored features for digital marketing agencies. Its robust EDR/XDR capabilities and real-time threat intelligence make it a top choice in endpoint security platforms, despite a higher price point and learning curve for non-technical users.
Pros
- 16-year Gartner Magic Quadrant Leader
- CryptoGuard rolls back ransomware encryption
- Synchronized Security isolates threats automatically
- Single pane of glass management
- Deep Learning AI malware detection
Cons
- High CPU usage during scans
- Slow performance on older hardware
- Steep learning curve for advanced features
- Support response times can be slow
- Reporting lacks granular customization
Best for teams that are
- Mid-sized businesses seeking effective, easy-to-manage ransomware protection [cite: 16]
- IT teams wanting a unified console for endpoint and network security [cite: 16]
Skip if
- Organizations needing highly granular, complex enterprise customization [cite: 17]
- Users frustrated by potential stability issues on macOS platforms [cite: 18]
Best for teams that are
- Mid-sized businesses seeking effective, easy-to-manage ransomware protection [cite: 16]
- IT teams wanting a unified console for endpoint and network security [cite: 16]
Skip if
- Organizations needing highly granular, complex enterprise customization [cite: 17]
- Users frustrated by potential stability issues on macOS platforms [cite: 18]
Pros
- 16-year Gartner Magic Quadrant Leader
- CryptoGuard rolls back ransomware encryption
- Synchronized Security isolates threats automatically
- Single pane of glass management
- Deep Learning AI malware detection
Cons
- High CPU usage during scans
- Slow performance on older hardware
- Steep learning curve for advanced features
- Support response times can be slow
- Reporting lacks granular customization
Expert Take
Sophos Endpoint Security is recognized for its advanced AI-powered protection and tailored features for digital marketing agencies. Its robust EDR/XDR capabilities and real-time threat intelligence make it a top choice in endpoint security platforms, despite a higher price point and learning curve for non-technical users.